ASUS is crossing the frontier between the digital and natural with its innovative ROG Mjolnir power station. Designed for gamers who crave boundless outdoor gaming, its name, inspired by both Norse myths and Marvel’s popular lore, is a statement of strength and adventure. Equipped with four AC outlets and four USB ports, this power station is not just a step toward a new demographic but a giant leap into uncharted territories.
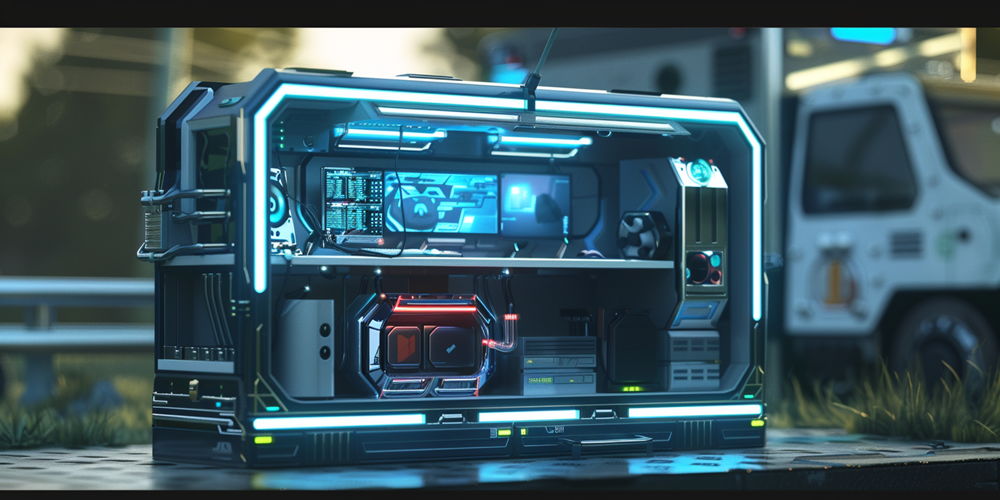
The ROG Mjolnir is an eye-catcher with its unique hammer shape, embodying ASUS’s dedication to revolutionizing gaming accessories. The inclusion of a large digital LCD pushes this innovation further, offering users a window into their power usage and the health of their connected devices. A testament to where tech is heading, the Mjolnir’s design plans for gamers’ lifestyles, seamlessly blending cutting-edge design with practical performance. With such advances, ASUS is setting the pace in a world where users demand their gadgets keep up with their dynamic lives.
An Innovative Leap for Gamers and Nature Enthusiasts Alike
The ROG Mjolnir could usher in a transformation in gaming, offering freedom from stationary setups. ASUS’s innovation promises to equip gamers with the capability to engage in high-end gaming anywhere, mirroring the independence smartphones gave to the workforce. Its impact may redefine gaming, making outdoor LAN events and tournaments possible without the constraint of fixed power sources.
The Mjolnir’s impact extends beyond technology—it fosters a more social gaming culture. Gamers could easily gather in any setting, from parks to woodlands, thanks to this visionary tool, adding an element of adventure to their gaming experiences. Anticipation for its reveal at Computex 2024 is high, as it promises to blend exploration with gaming, hinting at a trend where gaming can occur spontaneously, anywhere.