The recent groundbreaking AI-assisted eye surgery at Focus Clinics in London has set a new benchmark in medical technology, especially for individuals suffering from severe and complex vision disorders. Patrícia Gonçalves, a 31-year-old Portuguese woman with extreme astigmatism and near-sightedness, could only perceive the largest letters on an eye chart without corrective lenses. After undergoing this innovative procedure, her eyesight remarkably improved to 20/16, surpassing the average 20/20 vision. This revolutionary treatment underscores the incredible potential of artificial intelligence in transforming healthcare.
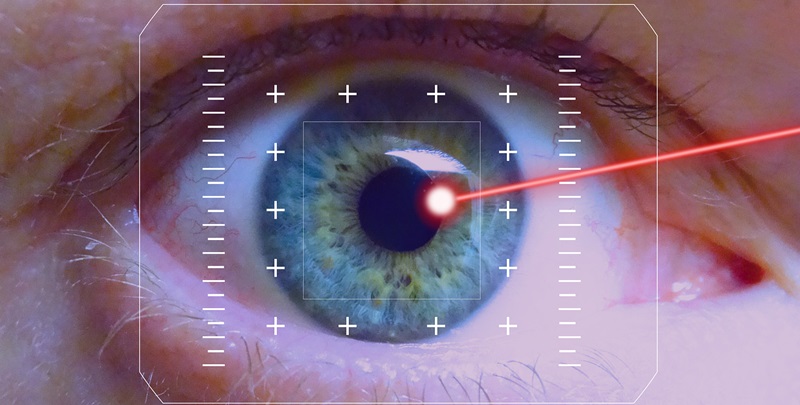
The surgery was made possible through an Eyevatar, a highly detailed digital model crafted from a 10-minute eye scan. Artificial intelligence played a pivotal role in determining the precise laser modifications needed to reconstruct Gonçalves’ corneas. Senior eye surgeon David Allamby emphasized the exceptional clarity of her vision post-surgery. Clinical studies included 200 patients, and every single one of them reported vision improvements, with some even achieving an astonishing 20/10 vision. This AI-driven approach not only sets a higher standard in vision correction but also showcases AI’s potential in offering highly personalized and effective healthcare solutions.
What makes this technology even more promising is its ability to refine the ‘Point Spread Function,’ a crucial measure of vision distortion, thus allowing for more precise and individualized treatments. Future implementations of this AI-assisted eye surgery are already planned for countries such as China and Australia. These countries are poised to benefit significantly from this cutting-edge technology, addressing the needs of many patients worldwide suffering from severe visual impairments.
In conclusion, the AI-assisted eye surgery performed at Focus Clinics marked a significant advancement in medical technology. It offered a glimpse into the revolutionary potential of AI in providing personalized and highly effective healthcare solutions. This development brought new hope to numerous patients globally dealing with severe vision issues and has likely paved the way for future innovations in the field of vision correction.