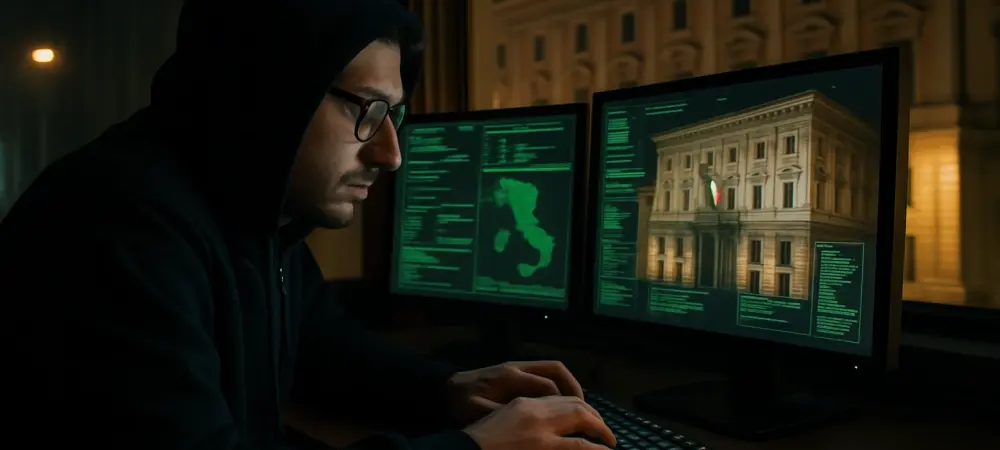
In an alarming revelation, cybersecurity firm Trellix has reported a sophisticated cyber espionage campaign targeting the Italian Ministry of Foreign Affairs. This breach has been linked to the India-based DoNot APT group, recognized for its long-standing focus on South Asian geopolitical interests. This latest campaign, however, marks a significant shift as the group broadens its scope to include European diplomatic targets. The operation showcases the group’s advanced multi-stage tactics designed not just to breach but to maintain long-term access to critical foreign governmental infrastructures for intelligence collection. These developments underscore the evolving threat landscape, where cyber espionage continues to pose a considerable risk to global diplomatic affairs.
Sophisticated Tactics and Diverse Methods
Multi-Stage Attack Strategy
The multi-stage attack involved clever deception, utilizing spear-phishing emails masquerading as communications from European defense officials. The emails contained links to a supposed Google Drive file, which was, in reality, a malicious RAR archive. Upon clicking, the malware was activated, embedding a persistent backdoor into the Ministry’s network. Such tactics reveal a high level of sophistication, highlighting the innovation and calculated risk-taking by the DoNot APT group. By appearing legitimate, these communications bypassed initial defenses, demonstrating the increasing difficulty traditional cybersecurity measures face against well-organized and cunning cybercriminal entities. The group’s use of tools, such as the LoptikMod malware, further underscores their technical capabilities. This malware, coupled with aggressive tactics like persistent scheduling tasks, ensured continuous access and allowed for prolonged data exfiltration. This approach not only reinforces their technical prowess but also signals a new era of cyber threats where attackers employ a blend of traditional methods with modern technological solutions to reach their goals. Trellix’s analysis emphasizes the critical need for organizations to reassess their cybersecurity posture, integrating advanced detection and response mechanisms to counter such insidious threats effectively.
Use of Legitimate Services for Malicious Purposes
Another striking aspect of this operation is the strategic exploitation of popular legitimate services like Google Drive, which adds another layer of credibility to the attackers’ communications. Since many governmental institutions are already predisposed to trust such platforms, the attackers used this trust to their advantage. By embedding malicious content within a commonly used service, they leveraged a sophisticated tactic requiring deep understanding of the target’s typical data handling and communication behaviors. This calculated move exemplifies their strategic dexterity and illustrates a broader trend of cyber actors adapting legitimate technologies for malicious purposes.
This method of attack makes it glaringly evident that the conventional boundaries of cybersecurity are continuously being tested and breached. The DoNot APT group’s ability to craftily integrate such services to disguise malicious intent signifies a dramatic elevation in the complexity of cyber threats. Institutions must recognize this shift and pursue robust analytical strategies and tools that can detect anomalies, leveraging AI and machine learning to differentiate between routine and suspect activities. Only with dynamic and adaptive security frameworks can organizations hope to fend off such innovative threats effectively.
The Broader Implications and Required Actions
Expansion of Cyber Espionage Targets
DoNot APT’s campaign against the Italian Ministry signals a noticeable shift in their operational focus, moving from their traditional South Asian interests to European diplomatic entities. This endeavor signifies not only a physical but a strategic expansion, identifying and exploiting weak links within newly targeted regions. The implications of this shift are profound, potentially sparking a new wave of similar actions against other European government agencies. Such campaigns could result in heightened geopolitical tensions and the potential compromise of sensitive governmental information. This observed trend calls for immediate international cooperative measures, reinforcing the collective cybersecurity infrastructure against such evolving threats. An increased focus on European targets by traditionally region-specific cybercriminal actors suggests a new paradigm in global cyber warfare. It emphasizes the urgent need for comprehensive cybersecurity policies that transcend national boundaries and foster shared intelligence and defense strategies. Building coalitions and sharing insights about common threats will amplify defensive capabilities and establish a more unified front against such advanced cyber adversaries.
Reinforcing Cybersecurity Defenses
In a concerning disclosure, the cybersecurity company Trellix has revealed an intricate cyber espionage campaign directed at the Italian Ministry of Foreign Affairs. The breach is attributed to the India-based DoNot APT group, distinguished by its persistent focus on geopolitical matters in South Asia. Nonetheless, this latest endeavor signals a notable shift as the group now extends its reach to European diplomatic targets. Their operation exemplifies the group’s sophisticated, multi-layered strategies aimed not only at infiltration but at preserving enduring access to vital foreign governmental systems for intelligence gathering purposes. Such developments highlight the continuously evolving threat landscape, where cyber espionage significantly endangers diplomatic engagements worldwide. Cyber threats are growing increasingly complex, emphasizing the urgent need for enhanced security measures and collaboration among nations to protect sensitive information and maintain international diplomatic stability.