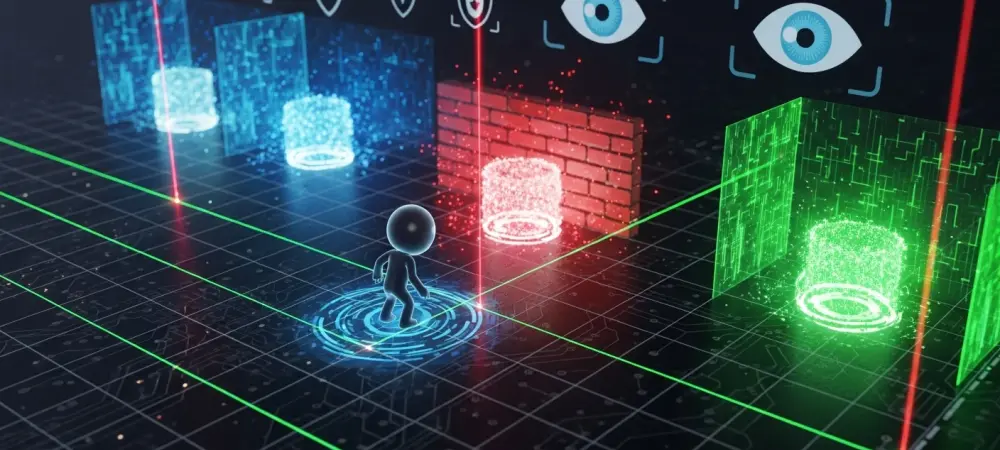
The clandestine proliferation of precision-engineered infostealers has fundamentally shifted the focus of cyber defense from blocking broad viral infections toward mitigating the surgical theft of session tokens and digital identities. Today, the cybersecurity environment faces a relentless surge in modular “infostealer” programs, with MicroStealer serving as the most prominent example of this specialized evolution. Unlike the destructive payloads of previous decades, these tools are designed for silent data harvesting, fueling a subterranean economy that prioritizes credentials over system disruption. The current market is defined by the Malware-as-a-Service model, allowing even low-skill actors to deploy high-impact campaigns against critical infrastructure. Within this ecosystem, major threat groups increasingly target the telecommunications and education sectors due to their vast repositories of sensitive user data. As regulations like GDPR and NIS2 continue to evolve, the rapid success of MicroStealer reveals a lingering disconnect between regulatory compliance and actual defensive resilience in the face of modern espionage.
Analyzing the Rise of MicroStealer and Infostealer Innovation
Emerging Trends in Social Engineering and Payload Delivery
Modern industry trends indicate a significant pivot away from traditional software exploits in favor of manipulating human psychology through sophisticated social engineering. MicroStealer demonstrates this evolution by utilizing reputable third-party hosting platforms like Dropbox or SourceForge, which allows the malicious payloads to inherit the inherent trust of these domains. By disguising itself as a legitimate game launcher or productivity tool, the malware bypasses initial scrutiny from both users and automated filters.
The integration of Electron-based wrappers further complicates detection, as these frameworks allow malicious code to blend seamlessly with modern web-based applications. This strategy moves the battleground from the network perimeter directly to the endpoint, where the distinction between a trusted update and a malicious injection has become increasingly blurred for the average employee. Consumers are targeted with high-fidelity lures that mimic popular software, marking a definitive departure from the generic phishing attempts seen in the past.
Market Projections: The Growth of Initial Access Brokerage
Current market data suggests that the demand for stolen session cookies and credentials has reached an unprecedented peak, with the sector for initial access brokerage expected to expand through 2028. Performance indicators gathered from global sandbox environments show that MicroStealer has achieved rapid market penetration across the United States and Germany, proving the scalability of its distribution model. This global reach highlights the effectiveness of using localized lures to target specific geographic regions with high concentrations of digital wealth. Forecasts indicate that as long as the resale value of session tokens remains high, malware families will continue to refine their exfiltration mechanisms. This high return on investment ensures that developers stay incentivized to produce more automated tools that can bypass multi-factor authentication by hijacking active browser sessions. The growth of this market is essentially a reflection of the transition toward a “token-based” economy, where access is often more valuable to a hacker than the data itself.
Overcoming the Challenges of Stealth and Evasion Techniques
The most daunting challenge currently facing the security industry is the widening detection gap caused by multi-stage execution chains and environment-aware code. MicroStealer utilizes the Nullsoft Scriptable Install System and bundled Java Runtime Environments to mask its intentions, appearing as a standard utility to traditional signature-based antivirus software. To effectively counter these obstacles, organizations have been forced to invest in resource-heavy defensive strategies that go beyond simple scanning. A major hurdle remains the malware’s ability to detect virtual machines and research environments, which effectively prevents defenders from documenting its behavior in a controlled setting. Overcoming this requires the implementation of bare-metal analysis and advanced behavioral heuristics that can identify subtle masquerading tactics. For example, the deliberate renaming of malicious processes to “miicrosoft.exe” is a classic technique used to blend into the background of system tasks, making manual discovery nearly impossible for an average user.
Navigating the Regulatory and Compliance Environment
Navigating the current regulatory environment has become more complex as MicroStealer renders traditional multi-factor authentication (MFA) insufficient for many compliance frameworks. Because the malware facilitates “Pass-the-Cookie” attacks, a simple password and SMS code no longer satisfy the security requirements of high-stakes environments like finance or healthcare. Consequently, regulators have begun pushing for the adoption of phishing-resistant MFA standards, such as FIDO2, to mitigate the risk of session hijacking.
Additionally, there is an expanding expectation for corporate responsibility regarding outbound traffic monitoring. Organizations are now scrutinized on their ability to identify and block unauthorized data flows to common platforms like Discord, which are frequently exploited for command-and-control communication. This shift reflects a broader trend where compliance is measured not just by internal controls, but by a company’s ability to monitor the entire lifecycle of its data as it moves toward external endpoints.
The Future of Infostealers and Defensive Innovation
The trajectory of the infostealer industry suggests a future dominated by increased automation and the dynamic integration of artificial intelligence to craft even more convincing lures. Future versions of MicroStealer will likely employ dynamic payload generation, ensuring that every individual infection possesses a unique file signature to frustrate even the most advanced automated detection tools. We are also seeing a shift toward targeting cloud-native environments and SaaS platforms directly, moving past the local machine to compromise entire enterprise ecosystems. Growth areas for the defense sector must focus on AI-driven Endpoint Detection and Response and the broader implementation of Zero Trust Architecture. By continuously verifying user identity and device health throughout a session, organizations can significantly reduce the impact of a single compromised credential or stolen token. The shift toward a posture that assumes breach is inevitable will be the only way to stay ahead of malware that evolves as quickly as the platforms it targets.
Summary of Findings: Strategic Recommendations for Resilience
The rise of MicroStealer underscored a critical turning point in the threat landscape where human-centric entry points and multi-stage execution paths proved highly effective against established defenses. It demonstrated that the telecommunications and education sectors remained vulnerable to specialized tools designed to exploit the gap between user trust and technical security. To build long-term resilience, organizations prioritized the deployment of behavioral monitoring tools and transitioned toward authentication methods that were inherently resistant to session theft.
Security teams also recognized the necessity of educating users on the dangers of third-party software distributors and the subtle signs of process masquerading. Ultimately, the industry moved toward a more proactive stance that valued visibility into outbound data flows and anomalies over the mere presence of signature-based defenses. These actions were essential in mitigating the risks posed by MicroStealer and prepared the global infrastructure for the next generation of digital identity theft. As developers continue to automate their tactics, the ability to maintain a continuous cycle of verification and monitoring became the definitive standard for enterprise protection.