Network security is crucial for the protection of an organization’s IT infrastructure, and any vulnerabilities within these systems pose a significant risk. ArubaOS, the operating system that powers Aruba Networks’ switches, is integral to the management of network traffic and data security. The discovery of critical vulnerabilities within ArubaOS is a cause for concern, as it potentially leaves networks open to attacks that could result in unauthorized access or service disruptions. It is imperative for network administrators and organizations to carefully monitor these vulnerabilities to reduce the risk of exploitation. Ensuring that ArubaOS operates securely is not only foundational to network performance but also critical for maintaining the trust and reliability stakeholders have in an organization’s technological capabilities.
The Severity of ArubaOS Vulnerabilities
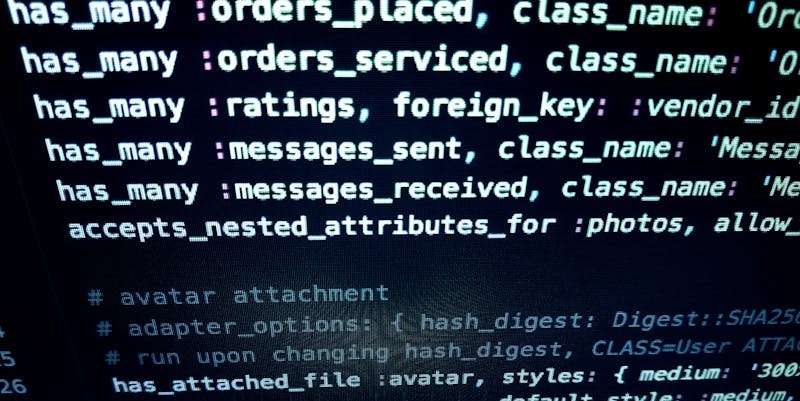
The discovery of serious vulnerabilities, such as CVE-2022-1356, CVE-2022-25611, CVE-2022-25612, and CVE-2022-25613, within ArubaOS, highlights a significant threat to network security. Attackers with authorized access to the Command Line Interface (CLI) could exploit these vulnerabilities to gain elevated permissions and execute arbitrary commands, leading to a compromised switch and unauthorized activities ranging from data theft to complete network disruption. These vulnerabilities have been assigned a high CVSSv3 score of 7.2, emphasizing the necessity of prompt patches and strict access control to mitigate the risk of damage.
Even vulnerabilities with a medium severity rating, such as CVE-2022-25614, can have a deep impact on network operations, enabling attackers to delete files and potentially lead to denial-of-service conditions or system integrity compromises. The consequences of such exploits can be severe, including operational downtime and the potential for data loss or corruption, affecting business continuity.
Immediate Actions and Long-term Strategies
In response to these vulnerabilities, HPE Aruba has issued patches for ArubaOS, highlighting the critical need for organizations to update their systems to the latest, secure versions to avoid cyberattacks. Even though active exploitation has not yet been reported, the public disclosure of these issues increases the likelihood of attacks. Administrators should expedite the patching process to safeguard their systems.
Moreover, strengthening network security infrastructures is paramount, requiring regular vulnerability assessments and the adoption of advanced security tools like Perimeter81. These practices are essential in defending against various forms of malware, including ransomware and zero-day attacks, particularly those targeting unpatched systems.
Employing cybersecurity best practices is equally important. Practices such as restricting access, implementing multi-factor authentication, and continuously educating staff can contribute to a more secure network. Through these measures, administrators are better equipped to address the risks associated with vulnerabilities in core systems like ArubaOS, improving overall network security.