The cyber realm is fraught with covert threats that insidiously undermine crucial systems globally. Central to these dangers is Earth Krahang, an Advanced Persistent Threat (APT) group with formidable capabilities. Having infiltrated government agencies and vital sectors across nations with an almost ghostlike presence, their actions bear the hallmark of a sophisticated nation-state entity. Earth Krahang operates with a level of precision and discretion that is alarmingly efficient, showcasing the dual role of governments in cyberspace—as defenders and potential adversaries. The existence of such groups underscores the intricate and shadowy world of cyber espionage and cyber warfare, highlighting the evolving nature of international security challenges in the digital age. Earth Krahang’s strategic incursions into confidential networks embody the complexity and covert nature of global cybersecurity threats that confront state actors and industries alike.
The Rise of Earth Krahang
Emerging from the cyber underworld, Earth Krahang has demonstrated its capabilities by targeting over 70 organizations across 23 countries. With a focus on governments, foreign affairs ministries, and critical sectors such as telecommunications and finance, the group epitomizes the new age of espionage — one that leverages digital prowess over traditional means. This section delves into the group’s initial ascent to infamy, outlining its primary targets, methods of attack, and the distinctive patterns in its cyber offensives.
The carefully selected targets reveal the group’s strategic focus on gathering intelligence and influencing global power dynamics. Their methodical approach includes spear-phishing campaigns to infiltrate networks, exploiting software vulnerabilities, and deploying customized malware to maintain prolonged access to sensitive information. Earth Krahang has not limited its endeavors to a single region, aiming for a diverse array of countries to maximize its reach and impact on foreign intelligence.
Demystifying the Intricate Web of Espionage
Zeroing in on Earth Krahang’s tactics, it becomes apparent that their strategies are not only effective but alarmingly covert. From spear-phishing emails to utilizing compromised inter-governmental trust, they embody the contemporary cyber spy. Trend Micro’s research unpacks the intricacies of such operations, offering readers a rare glimpse into the inner workings of state-aligned cyber operations. This understanding is critical for recognizing and mitigating similar threats in the cyber arena.
The sophistication of Earth Krahang’s approach reflects a deep understanding of their targets’ communications and behavior. Using deceptive emails that appear legitimate, they have been able to breach the defenses of even the most secure institutions. Once inside, they move laterally across the network, avoiding detection while they gather valuable data. Their careful planning and execution signify a new era of espionage where the keyboard is mightier than the sword.
The Art of Cyber Espionage
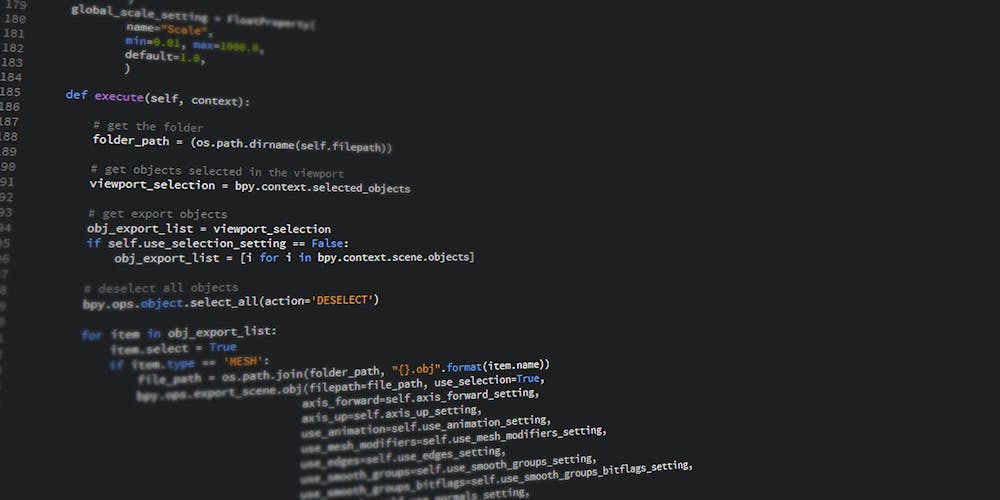
Behind Earth Krahang lies a mastery of both the technical and the psychological. Crafting believable phishing campaigns and exploiting software vulnerabilities are but a fraction of their arsenal. This section discusses the elaborate techniques deployed, encompassing the use of malware such as ShadowPad and the strategic deployment of backdoors, painting the picture of an adversary with vast technological resources and intelligence.
Efficient and pervasive, Earth Krahang utilizes a range of tools that are constantly being updated and refined to bypass modern security measures. Their repertoire includes ReShell, XDealer, Cobalt Strike, PlugX, and ShadowPad, each chosen for their specific utility in operation. The employment of these sophisticated tools underlines the group’s aim to remain undetected while they carefully mine networks for high-value information and maintain their grip on compromised systems for future operations.
The Earth Lusca Connection
The clandestine nature of cyber warfare often involves hiding in plain sight and collaborative endeavors among various actor hands. Earth Krahang is no standalone operation, as is evidenced by the connection to Earth Lusca and China’s Ministry of Public Security. This liaison details the layering of the cyber-espionage landscape and projects the alarming potential for even more sophisticated, state-sponsored cyber campaigns in the future.
The web of connections extends to I-Soon, a private contractor with allegiances to China, drawing a picture of an entangled web of actors within the nation-state’s cyber arsenal. The apparent overlap in infrastructure and toolsets between Earth Lusca and Earth Krahang suggests a coordinated division of labor, broadening the operational scope and efficiency of these cyber espionage campaigns. It’s a clear indicator of a deep, organized network with global reach and formidable capabilities.
Securing the Digital Battleground
Acknowledging the gravity of this cyber threat, Trend Micro calls for a fortified defensive strategy from organizations worldwide. By instilling robust cybersecurity measures, including employee awareness programs and advanced technical defenses, the article emphasizes the importance of preparedness in the face of such complex and sustained digital assaults. This section aims to equip the reader with the knowledge to defend against the machinations of groups like Earth Krahang.
Organizations are urged to vigilantly update and patch their systems, conduct regular security assessments, and promote cybersecurity awareness among staff. With human error often the weakest link, training employees to spot and react to phishing attempts is crucial. Furthermore, implementing multi-factor authentication, firewalls, and intrusion detection systems can act as additional layers of defense. A proactive stance against such APT groups is not just recommended, but essential for the preservation of national and corporate security.
A Wider Look at Cybersecurity Trends
The realm of cybersecurity is constantly under siege, not just from Earth Krahang’s campaigns but from a myriad of threats. Sophisticated malware, DDoS onslaughts, and the rise of enterprising cybercriminals mark today’s cybersecurity landscape. New firms are emerging to counter such threats, while nations draft laws to safeguard digital privacy.
Ransomware and data breaches are particularly prevalent, underscoring the diverse and serious nature of cyberattacks. With technological advancements, the risk surface widens, calling for ever-more agile and robust cyber defenses. It’s not just the work of nation-states but also autonomous hackers driven by profit or chaos. The cybersecurity domain demands unwavering alertness and evolving strategies to protect individuals and organizations across the globe from these digital dangers.