DevOps
- DevOps

The velocity of software production has reached a point where human intervention is no longer the primary driver of development, but rather the most significant bottleneck in the security lifecycle. As generative tools produce massive volumes of functional code in
- DevOps

The velocity of software production has reached a point where human intervention is no longer the primary driver of development, but rather the most significant bottleneck in the security lifecycle. As generative tools produce massive volumes of functional code in
Popular Stories
- DevOps

The velocity of software production has reached a point where human intervention is no longer the primary driver of development, but rather the most significant bottleneck in the security lifecycle. As generative tools produce massive volumes of functional code in
Deeper Sections Await
- DevOps
In the modern digital economy, grasping the intricacies of blockchain is vital. This revolutionary technology underpins significant shifts across various sectors, driving a need for individuals who can skillfully navigate its applications. Blockchain education equips professionals with the knowledge required
- DevOps

Centralized data repositories in IT Service Management (ITSM) systems introduce significant risks, acting as the system’s vulnerable core. They become prime targets for outages and cyber threats due to their centralized nature. These critical hubs, by concentrating resources and access
Browse Different Divisions
- DevOps
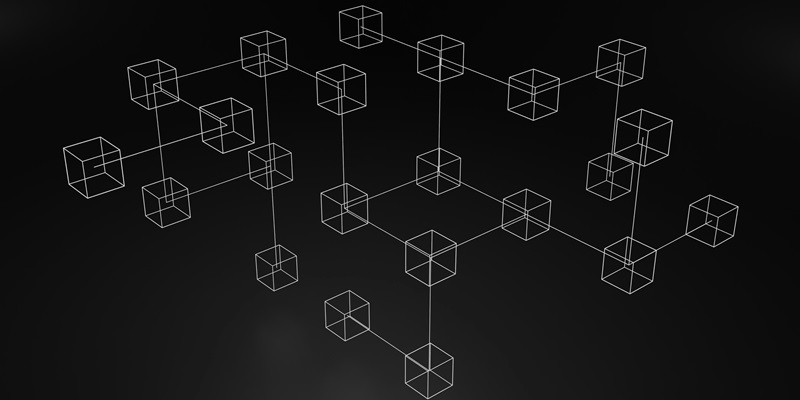
In the modern digital economy, grasping the intricacies of blockchain is vital. This revolutionary technology underpins significant shifts across various sectors, driving a need for individuals who can skillfully navigate its applications. Blockchain education equips professionals with the knowledge required
- DevOps

In the rapidly evolving tech industry, blockchain technology’s growing relevance cannot be overstated. It has become a pivotal force driving innovation across numerous sectors, making in-depth blockchain education an indispensable tool for tech professionals. This article delves into the reasons
- DevOps

The looming threat of quantum computing has prompted Ethereum co-founder Vitalik Buterin to propose a preemptive strike against such futuristic attacks. Recognizing that quantum computers could potentially decrypt current cryptographic systems, Buterin has outlined a mitigation strategy to safeguard Ethereum’s
- DevOps

With its sleek devices and user-friendly interface, Apple has become a symbol of innovation and sophistication in the technology industry. Yet, beneath the veneer of its success lies a potential threat to the very innovation that the tech world prizes.
- DevOps

Blockchain’s infusion in digital advertising heralds a potential revolution, promising to remedy the sector’s lingering woes such as obscurity, eroded confidence, and the inefficacy of current online ad systems. This technology is poised to catalyze a paradigm shift within the
- DevOps

Centralized data repositories in IT Service Management (ITSM) systems introduce significant risks, acting as the system’s vulnerable core. They become prime targets for outages and cyber threats due to their centralized nature. These critical hubs, by concentrating resources and access
Browse Different Divisions
Popular Stories
Uncover What’s Next