Cyber Security
- Cyber Security

The integrity of modern software development pipelines rests on the assumption that core version control operations are isolated from the underlying infrastructure governing repository storage. However, the recent discovery of a critical remote code execution vulnerability, identified as CVE-2026-3854, has
- Cyber Security

The integrity of modern software development pipelines rests on the assumption that core version control operations are isolated from the underlying infrastructure governing repository storage. However, the recent discovery of a critical remote code execution vulnerability, identified as CVE-2026-3854, has
Popular Stories
- Cyber Security

The recent confirmation of a sophisticated network intrusion at Medtronic has sent ripples through the medical technology sector, highlighting the persistent vulnerability of critical healthcare infrastructure in an increasingly digital world. This specific incident came to light after the notorious
Deeper Sections Await
- Cyber Security

The standard morning routine for millions of iPhone users shifted abruptly today when a persistent, high-priority alert bypassed the usual silence of Do Not Disturb to deliver a stark warning about imminent web-based attacks. This is not the typical understated
- Cyber Security

The moment a professional logs into their LinkedIn account to cultivate a network or research a career move, a silent digital probe may be cataloging the entire software environment of their personal computer without any visible warning. While most users
Browse Different Divisions
- Cyber Security

The standard morning routine for millions of iPhone users shifted abruptly today when a persistent, high-priority alert bypassed the usual silence of Do Not Disturb to deliver a stark warning about imminent web-based attacks. This is not the typical understated
- Cyber Security
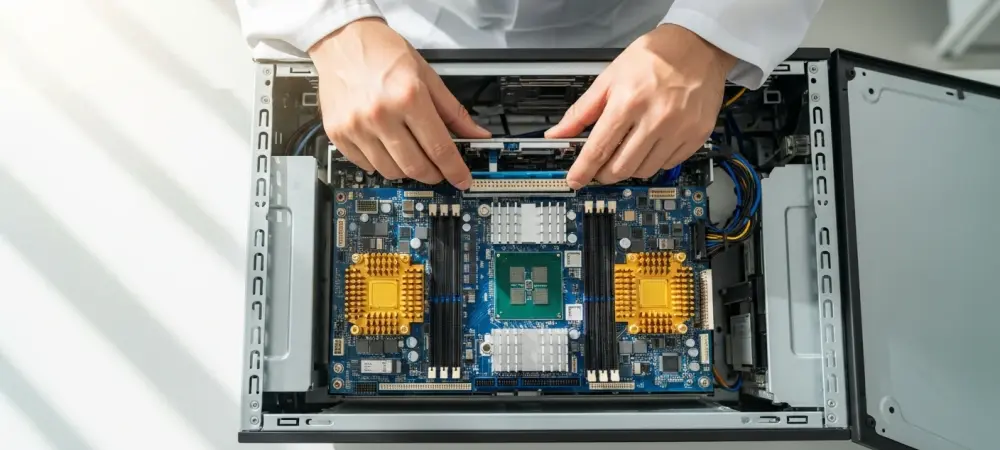
Modern digital infrastructure faces a relentless barrage of sophisticated threats that specifically target the core management layers of enterprise networks. When administrative tools like Cisco Integrated Management Controller (IMC) and Smart Software Manager (SSM) On-Prem exhibit vulnerabilities, the entire security
- Cyber Security

The digital perimeter that once defined corporate security has effectively dissolved, replaced by a complex web of interconnected services where a single minor oversight can trigger a catastrophic chain reaction across global infrastructures. While historical cyberattacks often relied on blunt
- Cyber Security

In an era where AI is moving from experimental labs to the heart of production systems, software supply chain security has become a high-stakes race between innovation and vulnerability. Dominic Jainy, an expert in the intersection of artificial intelligence and
- Cyber Security

Modern web browsing has transformed into a high-stakes environment where every click and search query serves as a data point for aggressive advertisers and sophisticated digital adversaries. As Chrome remains the dominant window to the online world, the necessity of
- Cyber Security

The moment a professional logs into their LinkedIn account to cultivate a network or research a career move, a silent digital probe may be cataloging the entire software environment of their personal computer without any visible warning. While most users
Browse Different Divisions
Popular Stories
Uncover What’s Next
















