Cyber Security
- Cyber Security

A seemingly simple oversight in a single line of code has created a significant security gap in over 300,000 WordPress websites, demonstrating how even popular and trusted tools can harbor critical vulnerabilities. This review explores the technical nature of the
- Cyber Security

A seemingly simple oversight in a single line of code has created a significant security gap in over 300,000 WordPress websites, demonstrating how even popular and trusted tools can harbor critical vulnerabilities. This review explores the technical nature of the
Popular Stories
- Cyber Security

A single vulnerability discovered within a global network of interconnected partners can methodically unravel decades of hard-won innovation and market leadership. The recent 1.4TB data breach at Nike, orchestrated by the “World Leaks” group, is not just an attack on
Deeper Sections Await
- Cyber Security

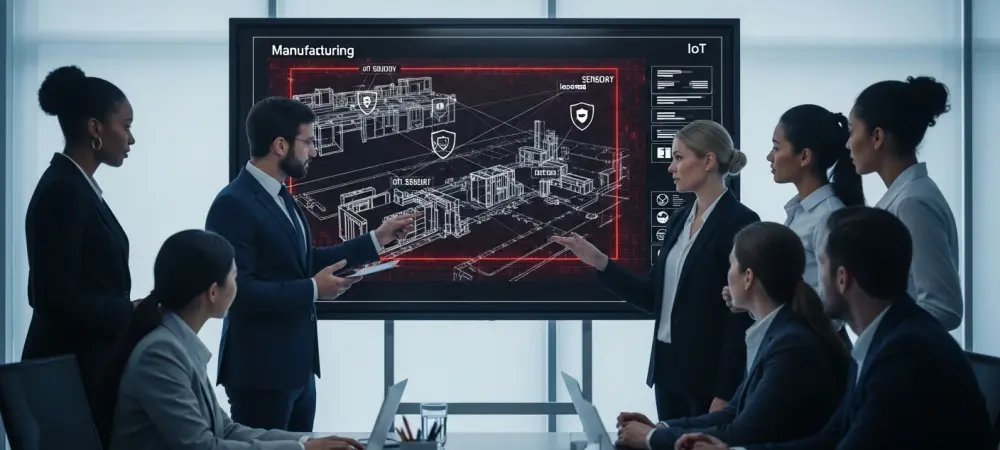
The Internet of Things (IoT) has rapidly infiltrated various industries, emerging as a pivotal component in operations ranging from agriculture to industrial control systems. While its significance grows, IoT’s security vulnerabilities present a pressing challenge. A substantial fraction of IoT
- Cyber Security

The network security landscape is experiencing an era of unprecedented challenges, as vulnerabilities in common networking devices like D-Link DIR-816 routers highlight glaring security gaps. These routers, which have been designated as End-of-Life, pose significant threats due to unpatchable vulnerabilities.
Browse Different Divisions
- Cyber Security

The Internet of Things (IoT) has rapidly infiltrated various industries, emerging as a pivotal component in operations ranging from agriculture to industrial control systems. While its significance grows, IoT’s security vulnerabilities present a pressing challenge. A substantial fraction of IoT
- Cyber Security

In a rapidly evolving digital landscape, the boundaries of cybersecurity are being tested by novel threats that defy conventional defenses. The discovery of Koske, an AI-assisted malware targeting Linux systems, marks a significant turning point in cyber threats. Identified by
- Cyber Security

In a recent move underscoring the relentless pursuit to safeguard cybersecurity infrastructure, Sophos and SonicWall have unveiled crucial patches aimed at addressing significant vulnerabilities in their products. These updates pertain to the Sophos Firewall and Secure Mobile Access (SMA) 100
- Cyber Security

In a world where cybercriminals constantly seek elusive techniques to bypass detection, the notion of bulletproof hosting gains palpable credence. Recent revelations have shown how cybercriminal networks globally manipulate these shady services, exemplified by cases like the Blind Eagle group
- Cyber Security

In an increasingly interconnected world where nations grapple for positions of influence, the shadowy realm of cyberspace often becomes the battlefield of choice. Imagine a scenario where sophisticated cyber exploits can subtly shift geopolitical power dynamics without firing a single
- Cyber Security

The network security landscape is experiencing an era of unprecedented challenges, as vulnerabilities in common networking devices like D-Link DIR-816 routers highlight glaring security gaps. These routers, which have been designated as End-of-Life, pose significant threats due to unpatchable vulnerabilities.
Browse Different Divisions
Popular Stories
Uncover What’s Next