Cyber Security
- Cyber Security

A sophisticated and sprawling financial underworld has quietly risen to prominence, leveraging the anonymity and speed of cryptocurrency to launder billions of dollars with alarming efficiency. A groundbreaking report reveals that Chinese Money Laundering Networks (CMLNs) now stand at the
- Cyber Security

A sophisticated and sprawling financial underworld has quietly risen to prominence, leveraging the anonymity and speed of cryptocurrency to launder billions of dollars with alarming efficiency. A groundbreaking report reveals that Chinese Money Laundering Networks (CMLNs) now stand at the
Popular Stories
- Cyber Security

A single vulnerability discovered within a global network of interconnected partners can methodically unravel decades of hard-won innovation and market leadership. The recent 1.4TB data breach at Nike, orchestrated by the “World Leaks” group, is not just an attack on
Deeper Sections Await
- Cyber Security

Imagine a world where a single malicious algorithm, powered by artificial intelligence, infiltrates a nation’s energy grid, shutting down power to millions in mere seconds, all orchestrated by an unseen adversary halfway across the globe. This isn’t science fiction—it’s a
- Cyber Security

Imagine a world where millions of phone calls, internet connections, and critical business operations grind to a halt overnight due to a single malicious act, and this nightmare became reality for Orange, France’s leading telecommunications provider. On July 25 of
Browse Different Divisions
- Cyber Security

Imagine a world where a single malicious algorithm, powered by artificial intelligence, infiltrates a nation’s energy grid, shutting down power to millions in mere seconds, all orchestrated by an unseen adversary halfway across the globe. This isn’t science fiction—it’s a
- Cyber Security
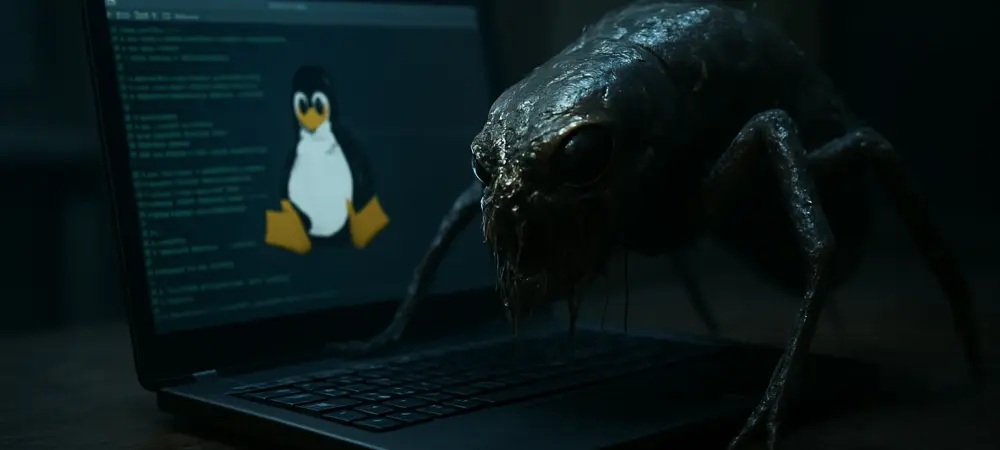
In a chilling development for cybersecurity professionals, a highly sophisticated Linux malware known as Plague has emerged as a formidable threat to critical infrastructure, slipping past traditional antivirus defenses with alarming ease and posing significant risks. Discovered by security researchers
- Cyber Security
Introduction to Fake Receipt Generators and Online Fraud Imagine purchasing a high-end gadget from a resale platform, only to discover later that the receipt provided as proof of authenticity is a complete fabrication, a scenario becoming alarmingly common as fake
- Cyber Security

Imagine a hidden menace lurking within an Android smartphone, capable of erasing every piece of personal data—photos, messages, and critical documents—without the user ever suspecting a thing. This chilling scenario is not a distant possibility but a present danger known
- Cyber Security
In a landscape where data breaches can cripple entire industries, a staggering statistic emerges: over 55,000 CrushFTP web interfaces are currently exposed online, as reported by Censys, making them potential targets for cybercriminals. This widely adopted file transfer software, integral
- Cyber Security

Imagine a world where millions of phone calls, internet connections, and critical business operations grind to a halt overnight due to a single malicious act, and this nightmare became reality for Orange, France’s leading telecommunications provider. On July 25 of
Browse Different Divisions
Popular Stories
Uncover What’s Next