Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security
Setting the Stage for Android Rooting Challenges Imagine a world where a single flaw in a widely used tool could unlock the deepest layers of millions of Android devices, handing over complete control to malicious actors, and this isn’t a
- Cyber Security

Imagine a scenario where a leading cloud-based platform, relied upon by thousands of businesses worldwide for customer relationship management, becomes a gateway for a sophisticated cyberattack, exposing critical vulnerabilities. This is the reality faced by Salesforce customers during a significant
Browse Different Divisions
- Cyber Security
Setting the Stage for Android Rooting Challenges Imagine a world where a single flaw in a widely used tool could unlock the deepest layers of millions of Android devices, handing over complete control to malicious actors, and this isn’t a
- Cyber Security

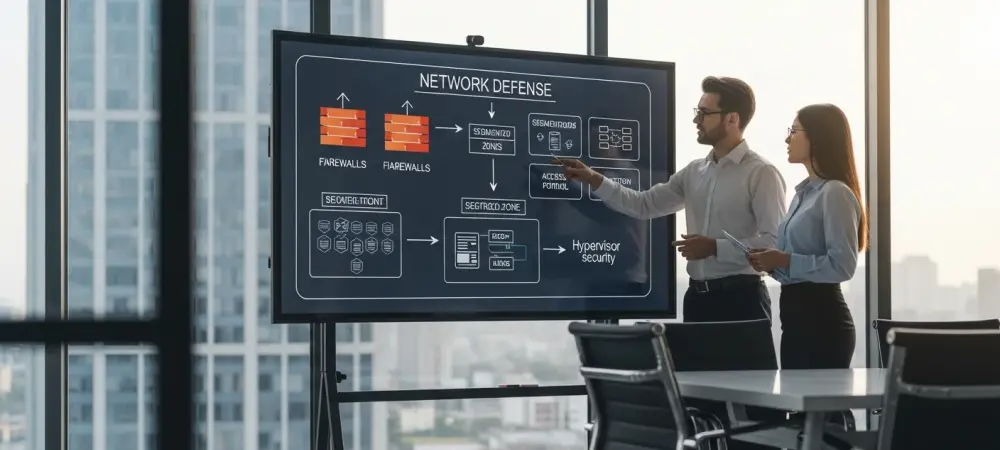
In an era where cyber threats loom larger than ever, with software supply chain attacks becoming a critical concern for both government and private sector entities, a groundbreaking solution has emerged to address these vulnerabilities head-on. The US Cybersecurity and
- Cyber Security

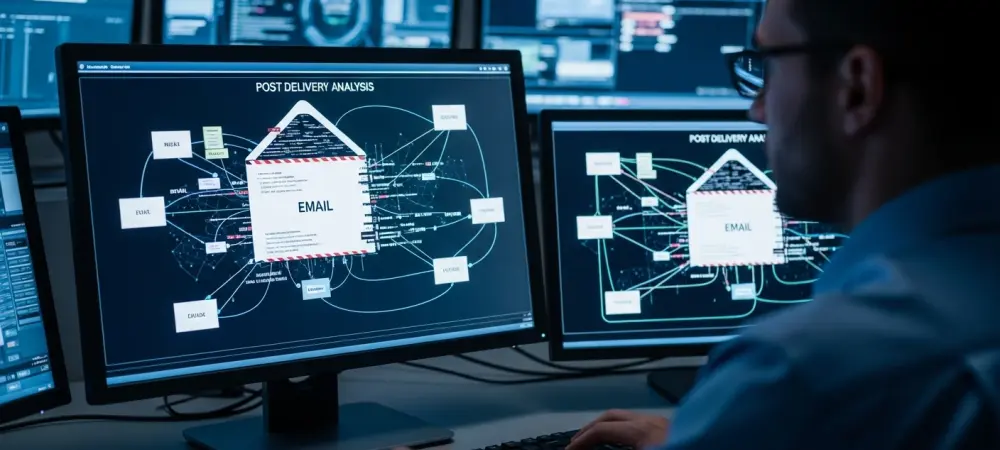
Imagine a scenario where a single breach in an on-premises server could silently grant attackers full control over a cloud-based email system, exposing sensitive data across an entire organization. This is not a hypothetical situation but a real threat posed
- Cyber Security

In an era where digital threats loom larger than ever, the battlefield of cybersecurity has shifted dramatically from purely technical defenses to the human element within organizations, highlighting a critical need for change. Cyber attackers no longer focus solely on
- Cyber Security

In an era where artificial intelligence shapes industries and innovation, a darker trend has emerged with cybercriminals leveraging advanced AI tools for malicious intent, as revealed by Anthropic’s Threat Intelligence reports. These reports highlight a disturbing reality: hackers are exploiting
- Cyber Security

Imagine a scenario where a leading cloud-based platform, relied upon by thousands of businesses worldwide for customer relationship management, becomes a gateway for a sophisticated cyberattack, exposing critical vulnerabilities. This is the reality faced by Salesforce customers during a significant
Browse Different Divisions
Popular Stories
Uncover What’s Next