Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

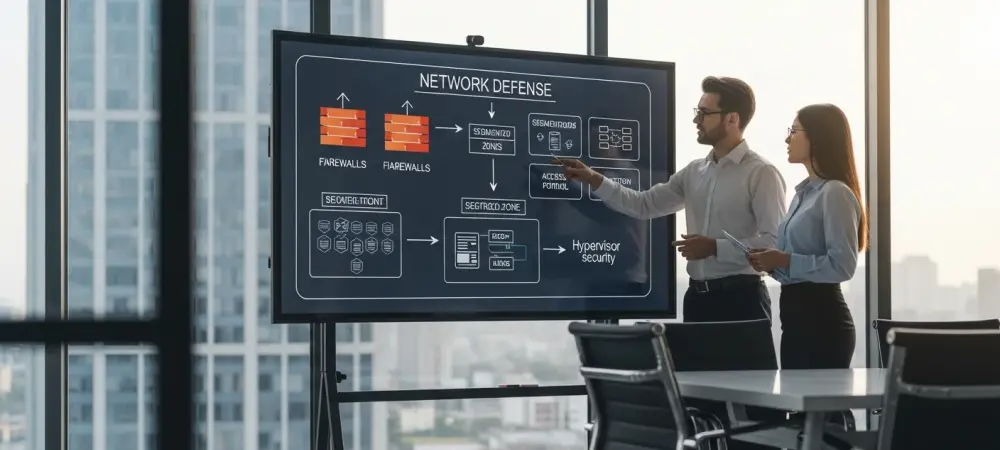
The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security

Imagine a scenario where an employee, searching for “Office 365” on a trusted search engine, clicks on what appears to be a legitimate ad, only to unknowingly surrender their Microsoft 365 credentials to cybercriminals through a flawless replica of the
- Cyber Security

In the ever-evolving landscape of cybersecurity, Security Information and Event Management (SIEM) systems stand as critical sentinels, tasked with monitoring, detecting, and responding to threats in real time across enterprise networks. Despite their pivotal role in safeguarding sensitive data and
Browse Different Divisions
- Cyber Security

Imagine a scenario where an employee, searching for “Office 365” on a trusted search engine, clicks on what appears to be a legitimate ad, only to unknowingly surrender their Microsoft 365 credentials to cybercriminals through a flawless replica of the
- Cyber Security

Imagine a world where your browser, powered by cutting-edge artificial intelligence, handles your online shopping, fills out forms, and even logs into your bank account without a second thought. This convenience, however, comes with a chilling downside: cybercriminals are now
- Cyber Security

Unveiling the AI-Driven Security Landscape In an era where cloud-native environments underpin nearly every enterprise operation, a staggering statistic emerges: cloud attacks now unfold in under 10 minutes, leaving no room for delay in defense mechanisms. As of 2025, artificial
- Cyber Security
Unveiling the Security Crisis in AI-Driven Coding Imagine a world where over 60% of software code is written not by human hands but by artificial intelligence, yet nearly every organization deploying this code faces a security breach due to inherent
- Cyber Security

A Digital Invasion Unfolds What happens when a nation’s most guarded secrets are just one click away from falling into enemy hands? In a chilling development, South Korean government and intelligence officials have become prime targets of a sophisticated spear-phishing
- Cyber Security

In the ever-evolving landscape of cybersecurity, Security Information and Event Management (SIEM) systems stand as critical sentinels, tasked with monitoring, detecting, and responding to threats in real time across enterprise networks. Despite their pivotal role in safeguarding sensitive data and
Browse Different Divisions
Popular Stories
Uncover What’s Next