Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

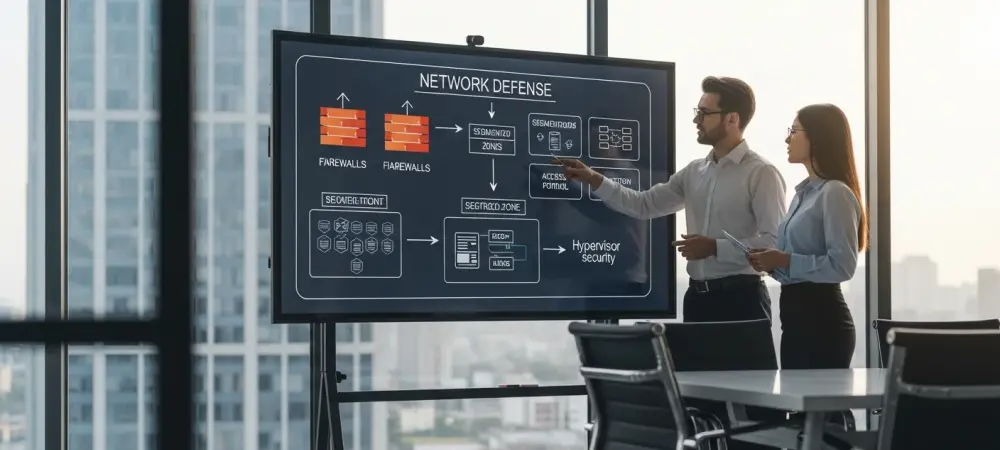
The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security

What happens when cyber threats evolve faster than security teams can respond, leaving businesses exposed to devastating breaches? In an era where digital attacks strike with unprecedented speed and sophistication, Arctic Wolf has introduced a game-changer: the AI Security Assistant.
- Cyber Security
Imagine a digital marketplace so vast that it serves billions of users worldwide, yet beneath its surface lurks a constant battle against hidden threats that jeopardize user safety. The Google Play Store, the primary app hub for Android devices, is
Browse Different Divisions
- Cyber Security

What happens when cyber threats evolve faster than security teams can respond, leaving businesses exposed to devastating breaches? In an era where digital attacks strike with unprecedented speed and sophistication, Arctic Wolf has introduced a game-changer: the AI Security Assistant.
- Cyber Security

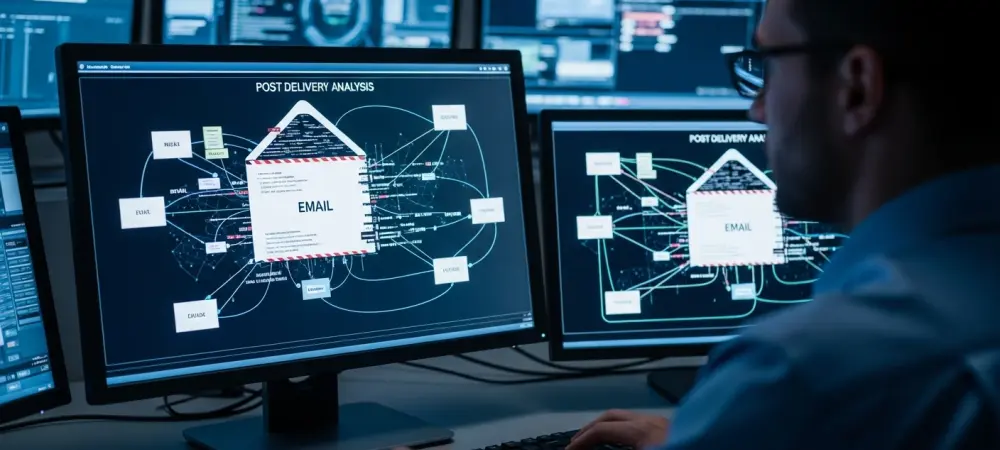
Imagine receiving an email that appears to come from within your own organization, complete with familiar branding and a sense of urgency about a voicemail you must retrieve, only to click on the attachment and unknowingly hand over your credentials
- Cyber Security

What happens when a single unprotected API endpoint becomes the gateway to a catastrophic data breach? In today’s hyper-connected digital landscape, where businesses rely on APIs to power everything from mobile apps to cloud services, the stakes have never been
- Cyber Security

Imagine a malicious software so advanced that it not only steals banking credentials but also locks devices for ransom and spies on every user interaction in real time, creating a chilling reality for mobile users. This terrifying threat has emerged
- Cyber Security

Unveiling the Threat Landscape of Modern Malware In an era where digital transactions underpin global economies, the specter of cybercrime looms larger than ever, with malware attacks striking at the heart of financial security. Imagine a single operation draining $28.5
- Cyber Security
Imagine a digital marketplace so vast that it serves billions of users worldwide, yet beneath its surface lurks a constant battle against hidden threats that jeopardize user safety. The Google Play Store, the primary app hub for Android devices, is
Browse Different Divisions
Popular Stories
Uncover What’s Next