Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

Law enforcement’s successful dismantling of major cybercriminal infrastructures often triggers an unforeseen evolutionary leap in the malware they target, a phenomenon starkly illustrated by the recent resurgence of the SystemBC botnet. This resilient network of compromised devices did not merely
Deeper Sections Await
- Cyber Security

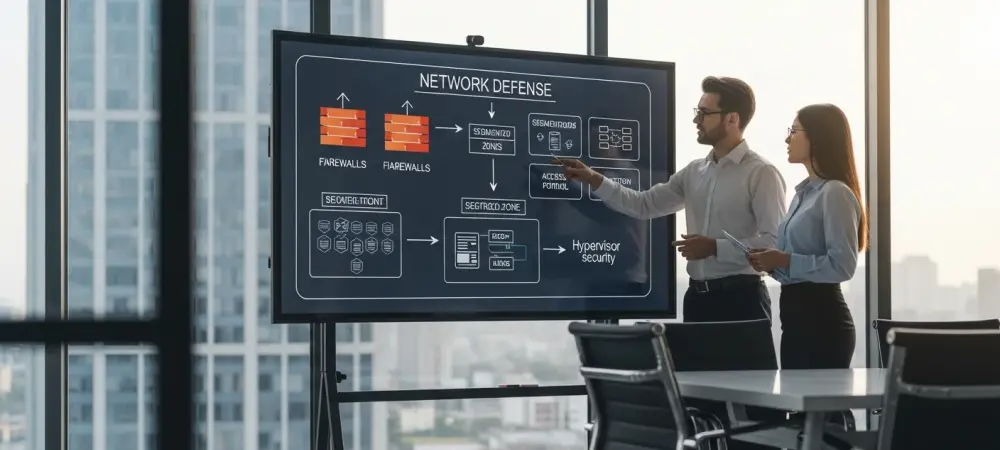
Introduction In an era where cyber threats evolve at an alarming pace, with ransomware and zero-day attacks targeting critical cloud workloads, the need for robust runtime security has never been more pressing. Imagine a system that not only detects anomalous
- Cyber Security

Setting the Stage for Gmail’s Security Challenges Imagine receiving a call from a number that appears to be Google’s official customer support, only to realize later that your Gmail account has been compromised, highlighting the growing sophistication of cybercriminals. This
Browse Different Divisions
- Cyber Security

Introduction In an era where cyber threats evolve at an alarming pace, with ransomware and zero-day attacks targeting critical cloud workloads, the need for robust runtime security has never been more pressing. Imagine a system that not only detects anomalous
- Cyber Security

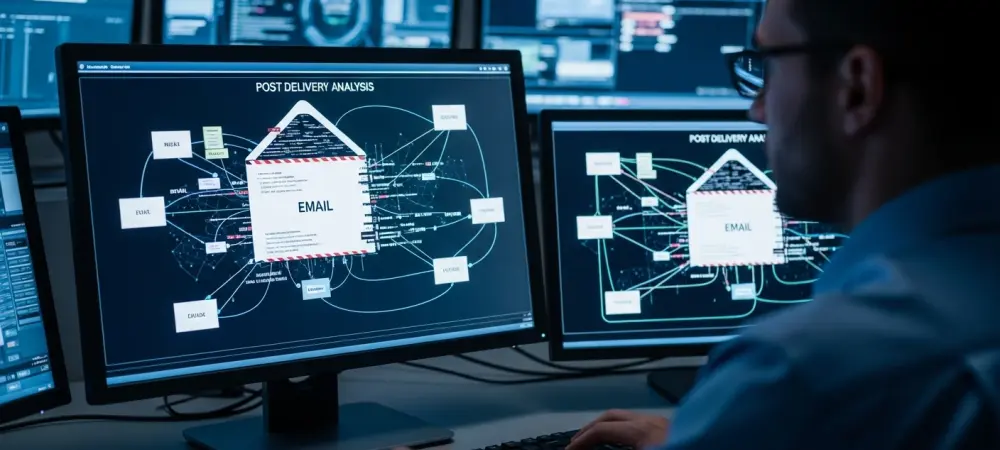
Introduction Imagine opening a seemingly harmless PDF attachment in an email, only to unknowingly unleash a devastating malware attack on an entire organization, a scenario that is becoming alarmingly common as cybercriminals increasingly exploit PDFs, a trusted file format, to
- Cyber Security

In an era where digital transactions dominate daily life, the alarming rise of data breaches casts a dark shadow over consumer trust, with incidents like the recent PayPal credential sale scare serving as a stark reminder of vulnerabilities in online
- Cyber Security

What happens when a technology hailed as the future of finance becomes a silent weapon in the hands of cybercriminals? In a startling revelation, Ethereum smart contracts—typically used for decentralized applications—have been hijacked to disguise malware targeting developers through npm
- Cyber Security
In a world where trust is the currency of diplomacy, what happens when an urgent email from a familiar embassy turns out to be a trap? Picture a high-ranking diplomat, pressed for time, clicking on a seemingly critical document only
- Cyber Security

Setting the Stage for Gmail’s Security Challenges Imagine receiving a call from a number that appears to be Google’s official customer support, only to realize later that your Gmail account has been compromised, highlighting the growing sophistication of cybercriminals. This
Browse Different Divisions
Popular Stories
Uncover What’s Next