Cyber Security
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
- Cyber Security

Beyond the headlines of conventional warfare, a persistent and clandestine conflict is unfolding across global networks, where nations deploy sophisticated digital operatives to harvest intelligence and secure geopolitical dominance. This escalating shadow war in cyberspace poses a direct and formidable
Popular Stories
- Cyber Security

The cybersecurity industry’s relentless pursuit of artificial intelligence and next-generation defenses often overshadows a stark and inconvenient truth: the most damaging breaches still exploit the most elementary security gaps. In an increasingly chaotic and complex threat landscape, a significant strategic
Deeper Sections Await
- Cyber Security

Introduction Imagine a hidden digital battlefield where malicious entities wield cutting-edge artificial intelligence to orchestrate attacks with unprecedented precision, only to have their covert operations laid bare by a single, unintended misstep. This scenario is not a distant possibility but
- Cyber Security

Introduction Imagine a world where every tap, swipe, and click on a smart device like an iPhone is silently recorded, not by a visible tracker, but by an invisible digital signature unique to each user, operating without explicit consent. This
Browse Different Divisions
- Cyber Security

Introduction Imagine a hidden digital battlefield where malicious entities wield cutting-edge artificial intelligence to orchestrate attacks with unprecedented precision, only to have their covert operations laid bare by a single, unintended misstep. This scenario is not a distant possibility but
- Cyber Security

I’m thrilled to sit down with Dominic Jainy, a seasoned IT professional whose deep expertise in artificial intelligence, machine learning, and blockchain offers a unique perspective on emerging cybersecurity threats. With a passion for exploring how cutting-edge technologies intersect with
- Cyber Security

In the ever-evolving landscape of cybersecurity, staying ahead of threats like ransomware is a top priority for organizations worldwide. Today, we’re thrilled to sit down with Dominic Jainy, an IT professional with deep expertise in artificial intelligence, machine learning, and
- Cyber Security

In an era where digital dependency shapes global business, a staggering revelation emerges: over 60% of enterprises with significant social media presence have faced targeted cyberthreats in the past year alone. Among these, a particularly insidious campaign known as Noodlophile
- Cyber Security

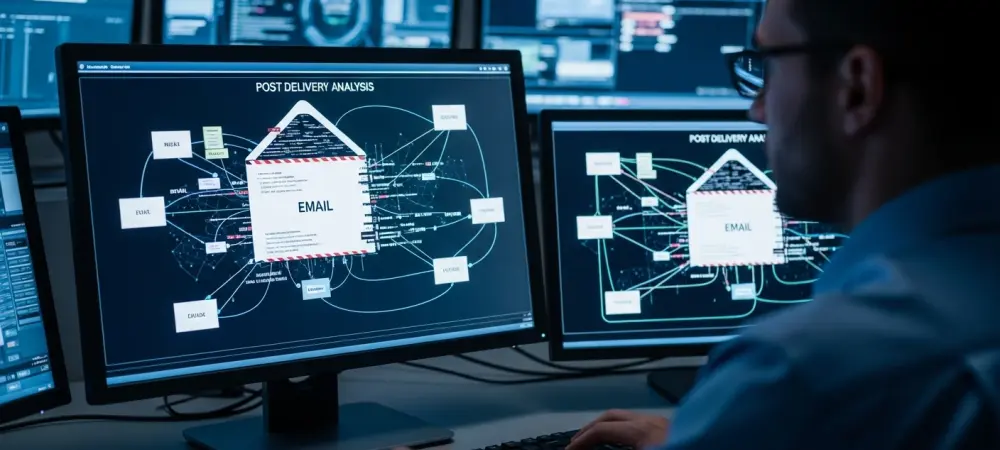
As cybercriminals grow more sophisticated with AI and social engineering, email remains a critical vulnerability for organizations worldwide. Today, we’re joined by Dominic Jainy, an IT professional with deep expertise in cutting-edge technologies like artificial intelligence, machine learning, and blockchain.
- Cyber Security

Introduction Imagine a world where every tap, swipe, and click on a smart device like an iPhone is silently recorded, not by a visible tracker, but by an invisible digital signature unique to each user, operating without explicit consent. This
Browse Different Divisions
Popular Stories
Uncover What’s Next