Cyber Security
- Cyber Security

Modern security operations now rely on a delicate web of interconnected applications where a single failure in identity validation can collapse the entire defensive perimeter of a global enterprise. As organizations rush to unify their communication channels with automated response
- Cyber Security

Modern security operations now rely on a delicate web of interconnected applications where a single failure in identity validation can collapse the entire defensive perimeter of a global enterprise. As organizations rush to unify their communication channels with automated response
Popular Stories
- Cyber Security
While traditional corporate firewalls remain formidable barriers, state-sponsored cyber operatives have discovered that the humblest pieces of hardware in a remote employee’s home often serve as the most effective backdoors into secure government and commercial networks. This realization has fueled
Deeper Sections Await
- Cyber Security

A Stark Reminder of Corporate Vulnerabilities In the high-stakes world of technology, where intellectual property often defines market dominance, a single data breach can send shockwaves through an entire industry, as seen in the staggering case at Intel. A former
- Cyber Security

In an era where cyber threats evolve at an alarming pace, a staggering number of organizations rely on Cisco systems for their networking and security infrastructure, only to find themselves at the mercy of newly discovered vulnerabilities that could compromise
Browse Different Divisions
- Cyber Security

A Stark Reminder of Corporate Vulnerabilities In the high-stakes world of technology, where intellectual property often defines market dominance, a single data breach can send shockwaves through an entire industry, as seen in the staggering case at Intel. A former
- Cyber Security

In an era where cyber threats loom larger than ever, with a staggering 147 billion threats blocked globally in a single year according to Trend Micro, the urgency for robust cybersecurity solutions has reached a critical juncture, demanding immediate attention
- Cyber Security
In today’s hyper-connected workplaces, a silent battle rages—one where artificial intelligence (AI) powers both the attackers and the defenders, creating a complex landscape of risk and opportunity. Picture a scenario where a single AI-crafted phishing email slips past traditional security,
- Cyber Security

In an era where cyber threats loom larger than ever, public entity risk pools in the United States face an uphill battle to protect diverse organizations like schools and local governments from digital dangers. A staggering report from recent cybersecurity
- Cyber Security
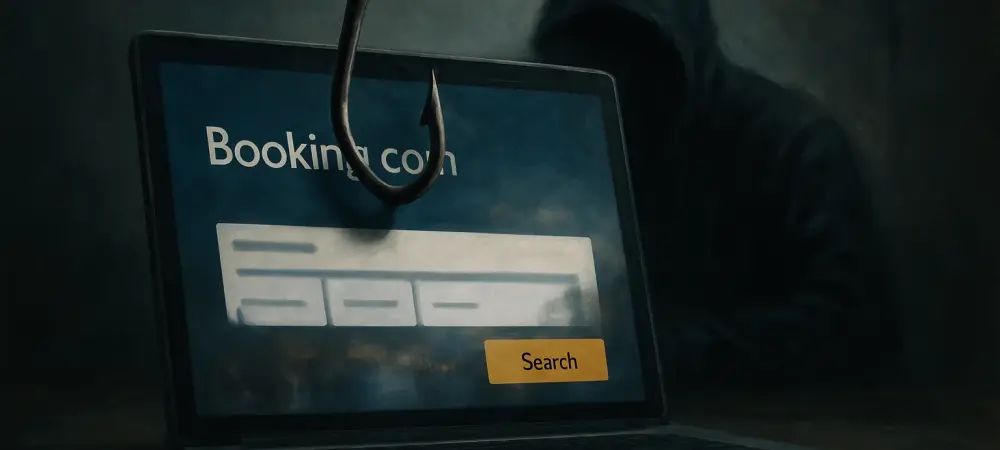
Introduction In an era where digital transactions dominate the travel industry, a staggering cybercrime wave has emerged, with millions of dollars stolen through deceptive tactics aimed at unsuspecting hotel guests and booking platforms. This alarming situation involves a sophisticated phishing
- Cyber Security

In an era where cyber threats evolve at an alarming pace, a staggering number of organizations rely on Cisco systems for their networking and security infrastructure, only to find themselves at the mercy of newly discovered vulnerabilities that could compromise
Browse Different Divisions
Popular Stories
Uncover What’s Next