Cyber Security
- Cyber Security
The digital silence of the networking giant was shattered when a notorious hacking collective announced they had bypassed the defenses of one of the world’s most influential technology firms. In late March, the group known as ShinyHunters issued a chilling
- Cyber Security
The digital silence of the networking giant was shattered when a notorious hacking collective announced they had bypassed the defenses of one of the world’s most influential technology firms. In late March, the group known as ShinyHunters issued a chilling
Popular Stories
- Cyber Security

Modern security operations centers are frequently paralyzed by a relentless flood of alerts that transforms the strategic process of escalation into a desperate survival mechanism rather than a path toward resolution. When the volume of incoming telemetry outpaces the cognitive
Deeper Sections Await
- Cyber Security

Imagine receiving a text message from what appears to be a trusted toll service, urging you to pay an overdue fee via a provided link. Unbeknownst to many, clicking that link could lead to a trap set by a sophisticated
- Cyber Security

Imagine a shadowy collective of hackers meticulously combing through professional networks, piecing together personal details of unsuspecting high-tech employees to expose them as targets in a digital war. This isn’t science fiction—it’s the reality of a sophisticated campaign by the
Browse Different Divisions
- Cyber Security

Imagine receiving a text message from what appears to be a trusted toll service, urging you to pay an overdue fee via a provided link. Unbeknownst to many, clicking that link could lead to a trap set by a sophisticated
- Cyber Security

Imagine a world where a seemingly harmless email attachment slips past every antivirus program, only to morph into a destructive force that adapts to every defense thrown at it. This isn’t science fiction—it’s the chilling reality of AI-augmented malware, a
- Cyber Security

Imagine a world where AI systems don’t just analyze data but independently make decisions, execute complex workflows, and drive innovation across enterprises with minimal human input. This isn’t a distant dream but the reality of agentic AI, a transformative force
- Cyber Security
Picture a massive enterprise with thousands of employees, each accessing critical systems daily, only to discover that a single overlooked software flaw could hand over the keys to malicious hackers. This is not a hypothetical nightmare but a pressing reality
- Cyber Security
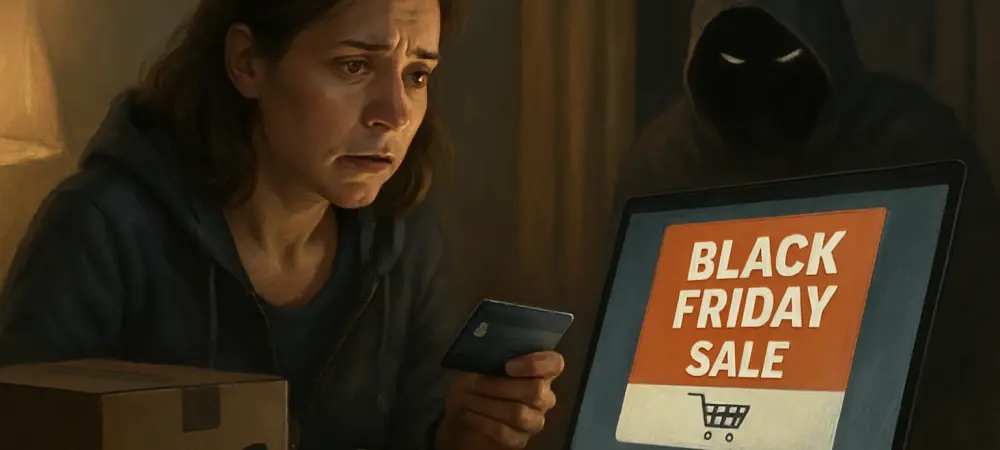
Imagine eagerly awaiting a Black Friday deal from Amazon, only to click on an email promising a steep discount and find yourself locked out of your account, your personal data stolen. This nightmare scenario is becoming all too common as
- Cyber Security

Imagine a shadowy collective of hackers meticulously combing through professional networks, piecing together personal details of unsuspecting high-tech employees to expose them as targets in a digital war. This isn’t science fiction—it’s the reality of a sophisticated campaign by the
Browse Different Divisions
Popular Stories
Uncover What’s Next