Cyber Security
- Cyber Security

The rapid acceleration of artificial intelligence across the global business landscape has created a peculiar architectural dilemma where the speed of innovation is frequently throttled by the necessity of digital safety. As organizations transition from experimental pilots to full-scale deployments,
- Cyber Security

The rapid acceleration of artificial intelligence across the global business landscape has created a peculiar architectural dilemma where the speed of innovation is frequently throttled by the necessity of digital safety. As organizations transition from experimental pilots to full-scale deployments,
Popular Stories
- Cyber Security

Modern security operations centers are frequently paralyzed by a relentless flood of alerts that transforms the strategic process of escalation into a desperate survival mechanism rather than a path toward resolution. When the volume of incoming telemetry outpaces the cognitive
Deeper Sections Await
- Cyber Security
In a world increasingly captivated by the promise of artificial intelligence, a coalition of international governments has delivered a sobering but necessary message to the stewards of the world’s most essential services: proceed with caution. This landmark initiative, spearheaded by
- Cyber Security

The fundamental trust developers place in open-source code has been systematically weaponized, transforming shared libraries from collaborative building blocks into delivery mechanisms for sophisticated threats like the recent “Shai Hulud v2” campaign. This new reality underscores a critical vulnerability at
Browse Different Divisions
- Cyber Security
In a world increasingly captivated by the promise of artificial intelligence, a coalition of international governments has delivered a sobering but necessary message to the stewards of the world’s most essential services: proceed with caution. This landmark initiative, spearheaded by
- Cyber Security
The long-anticipated integration of truly agentic artificial intelligence into mainstream web browsers is no longer a futuristic concept, representing one of the most significant evolutions in user-facing technology since the advent of the graphical interface itself. This review will explore
- Cyber Security

A tool designed to revolutionize software development by accelerating coding with advanced artificial intelligence became an open gateway for cybercriminals, exposing a critical flaw in the very foundation of modern AI tools within a single day of its launch. The
- Cyber Security
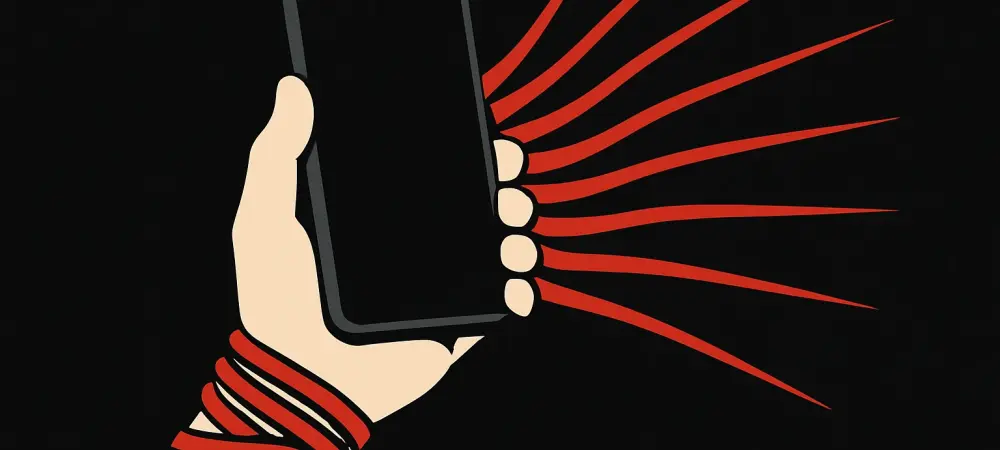
Introduction The personal data stored on a smartphone represents a detailed map of an individual’s life, a reality that makes the prospect of unauthorized access a deeply unsettling violation of privacy and security. In light of this, a recent notification
- Cyber Security

The contemporary cybersecurity landscape is in a state of constant, high-velocity flux, where the time between the discovery of a critical software flaw and its widespread weaponization by malicious actors has compressed dramatically, shifting the entire paradigm for digital defense.
- Cyber Security

The fundamental trust developers place in open-source code has been systematically weaponized, transforming shared libraries from collaborative building blocks into delivery mechanisms for sophisticated threats like the recent “Shai Hulud v2” campaign. This new reality underscores a critical vulnerability at
Browse Different Divisions
Popular Stories
Uncover What’s Next