Cyber Security
- Cyber Security

Modern security operations centers are frequently paralyzed by a relentless flood of alerts that transforms the strategic process of escalation into a desperate survival mechanism rather than a path toward resolution. When the volume of incoming telemetry outpaces the cognitive
- Cyber Security

Modern security operations centers are frequently paralyzed by a relentless flood of alerts that transforms the strategic process of escalation into a desperate survival mechanism rather than a path toward resolution. When the volume of incoming telemetry outpaces the cognitive
Popular Stories
- Cyber Security

Modern security operations centers are frequently paralyzed by a relentless flood of alerts that transforms the strategic process of escalation into a desperate survival mechanism rather than a path toward resolution. When the volume of incoming telemetry outpaces the cognitive
Deeper Sections Await
- Cyber Security
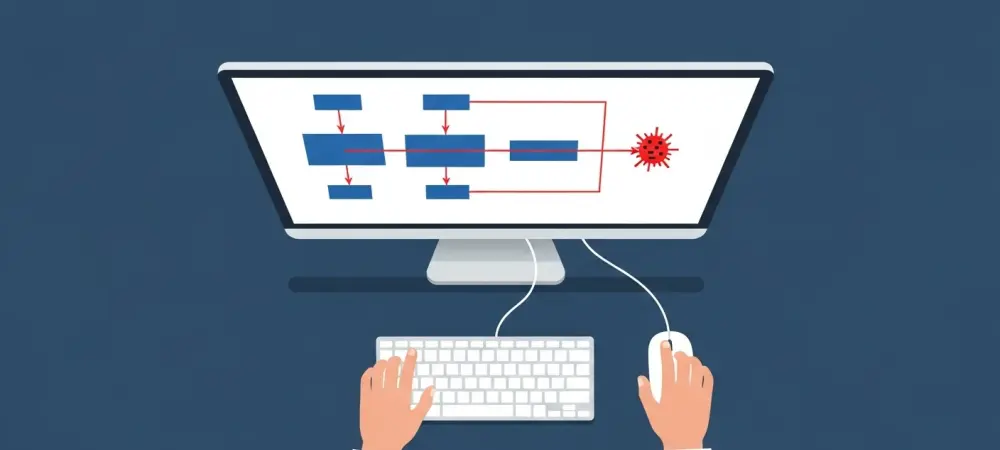
An Evolving Security Crisis in the React Ecosystem The global developer community is grappling with a rapidly escalating security dilemma as React releases critical patches for newly discovered flaws while state-sponsored threat actors simultaneously exploit a pre-existing, catastrophic vulnerability. This
- Cyber Security
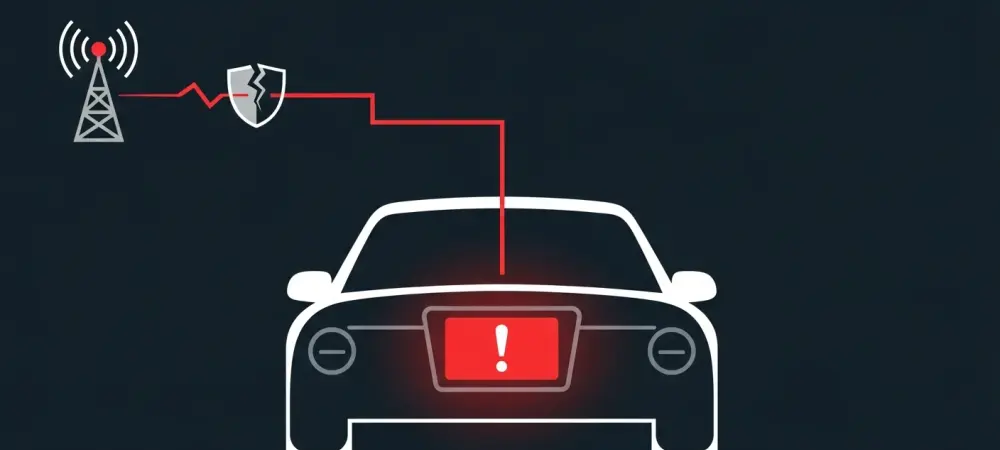
A recently uncovered security vulnerability in a widely used automotive component has transformed theoretical concerns into a tangible reality, demonstrating how hackers can remotely seize complete control of a vehicle’s dashboard infotainment system. This discovery serves as a stark reminder
Browse Different Divisions
- Cyber Security
An Evolving Security Crisis in the React Ecosystem The global developer community is grappling with a rapidly escalating security dilemma as React releases critical patches for newly discovered flaws while state-sponsored threat actors simultaneously exploit a pre-existing, catastrophic vulnerability. This
- Cyber Security

As digital threats against the nation’s most essential services grow increasingly sophisticated and interconnected, the need for a unified and actionable cybersecurity framework has never been more acute. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has responded to this
- Cyber Security
The ubiquitous black-and-white squares of QR codes, once symbols of convenient access to information, have been insidiously repurposed into a potent delivery mechanism for sophisticated cyberattacks. The use of weaponized QR codes in mobile malware campaigns represents a significant evolution
- Cyber Security
The trust inherent in academic collaboration has been dangerously weaponized in a new wave of cyber espionage, where the intellectual capital of scholars is now the primary target for state-sponsored threat actors. A sophisticated campaign uncovered in October 2025 demonstrates
- Cyber Security
In the high-stakes world of cybersecurity, every second counts. For the analysts on the front lines in a Security Operations Center (SOC), the time between an initial alert and a final verdict is a critical window where a minor threat
- Cyber Security
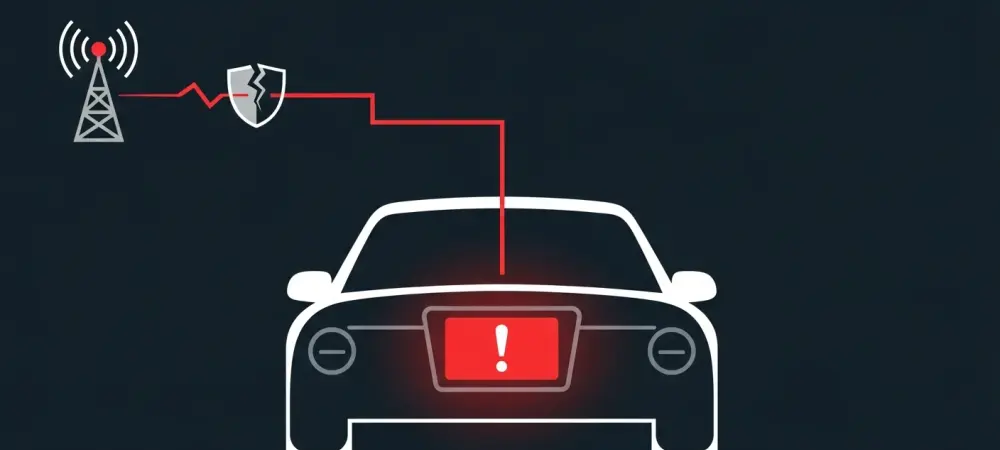
A recently uncovered security vulnerability in a widely used automotive component has transformed theoretical concerns into a tangible reality, demonstrating how hackers can remotely seize complete control of a vehicle’s dashboard infotainment system. This discovery serves as a stark reminder
Browse Different Divisions
Popular Stories
Uncover What’s Next