Cyber Security
- Cyber Security

Dominic Jainy is a seasoned IT professional with a deep specialization in artificial intelligence, machine learning, and blockchain. With years of experience navigating the complexities of emerging technologies, he has become a respected voice on how advanced AI models reshape
- Cyber Security

Dominic Jainy is a seasoned IT professional with a deep specialization in artificial intelligence, machine learning, and blockchain. With years of experience navigating the complexities of emerging technologies, he has become a respected voice on how advanced AI models reshape
Popular Stories
- Cyber Security

A single, unsuspecting click on a seemingly routine password reset notification recently managed to dismantle a multi-billion-dollar retail empire in a matter of hours. This spear-phishing incident did not just leak data; it triggered a sophisticated ransomware wave that paralyzed
Deeper Sections Await
- Cyber Security
A recently uncovered automated campaign, dubbed PCPcat, has demonstrated the alarming velocity of modern cyberattacks by successfully compromising over 59,000 internet-facing Next.js servers in a mere 48-hour window. This incident serves as a critical benchmark for understanding the current threat
- Cyber Security
The very memory that powers modern databases can sometimes become an unintentional treasure trove for attackers, silently exposing an organization’s most sensitive secrets to the outside world. A recently discovered vulnerability, known as MongoBleed, brings this abstract threat into sharp
Browse Different Divisions
- Cyber Security
A recently uncovered automated campaign, dubbed PCPcat, has demonstrated the alarming velocity of modern cyberattacks by successfully compromising over 59,000 internet-facing Next.js servers in a mere 48-hour window. This incident serves as a critical benchmark for understanding the current threat
- Cyber Security
The subtle imperfections that once betrayed a phishing email, such as grammatical errors or awkward phrasing, are rapidly disappearing in an age where artificial intelligence can craft flawless and highly persuasive deceptions. This shift marks a new chapter in cybercrime,
- Cyber Security

While enterprise security teams were winding down for the Christmas holiday, a sophisticated threat actor launched an expansive automated campaign, unleashing over 2.5 million malicious requests against a wide array of web applications worldwide. The operation, characterized by its scale
- Cyber Security

The very headphones designed to deliver private audio experiences to millions of users worldwide have been found to contain a critical flaw that can turn them into a gateway for hijacking connected smartphones. A groundbreaking investigation has uncovered a series
- Cyber Security
The common narrative surrounding cybercrime often portrays threat actors as ghost-like figures, executing flawless, automated campaigns that bypass defenses with surgical precision, but a detailed examination of the digital residue left behind on compromised systems paints a dramatically different and
- Cyber Security
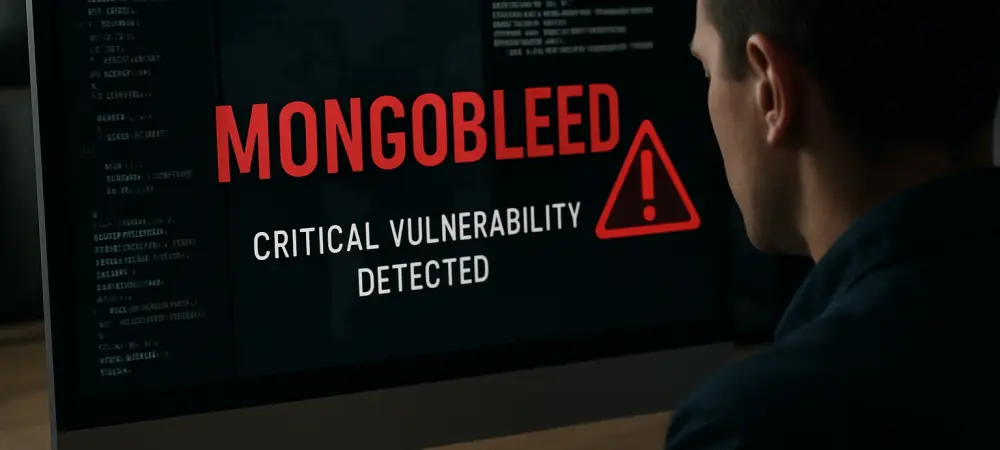
The very memory that powers modern databases can sometimes become an unintentional treasure trove for attackers, silently exposing an organization’s most sensitive secrets to the outside world. A recently discovered vulnerability, known as MongoBleed, brings this abstract threat into sharp
Browse Different Divisions
Popular Stories
Uncover What’s Next