Cyber Security
- Cyber Security

The rapid integration of Large Language Models into the modern enterprise stack has essentially redrawn the map of cyber warfare by exposing the fragile underpinnings of the software supply chain. While productivity gains have been undeniable, the rush to adopt
- Cyber Security

The rapid integration of Large Language Models into the modern enterprise stack has essentially redrawn the map of cyber warfare by exposing the fragile underpinnings of the software supply chain. While productivity gains have been undeniable, the rush to adopt
Popular Stories
- Cyber Security

A single, unsuspecting click on a seemingly routine password reset notification recently managed to dismantle a multi-billion-dollar retail empire in a matter of hours. This spear-phishing incident did not just leak data; it triggered a sophisticated ransomware wave that paralyzed
Deeper Sections Await
- Cyber Security

A newly disclosed vulnerability within a widely used audio component has prompted an urgent security advisory, potentially exposing millions of Android devices to remote code execution attacks if left unpatched. The January 2026 Android Security Bulletin from Google brings to
- Cyber Security

The very technologies celebrated for catapulting manufacturing into a new era of unprecedented efficiency are the same ones that have tragically made it the world’s most consistent target for cyberattacks. For years, the sector operated behind the perceived safety of
Browse Different Divisions
- Cyber Security

A newly disclosed vulnerability within a widely used audio component has prompted an urgent security advisory, potentially exposing millions of Android devices to remote code execution attacks if left unpatched. The January 2026 Android Security Bulletin from Google brings to
- Cyber Security

Today we’re sitting down with Dominic Jainy, an IT professional whose expertise spans artificial intelligence, machine learning, and blockchain. Given his deep understanding of how modern technologies intersect, he’s the perfect person to help us unravel the complexities of a
- Cyber Security
In a landmark decision that pries open the typically opaque world of artificial intelligence development, a federal court has mandated that OpenAI must produce a staggering 20 million anonymized user conversations from its ChatGPT service. This pivotal ruling, handed down
- Cyber Security

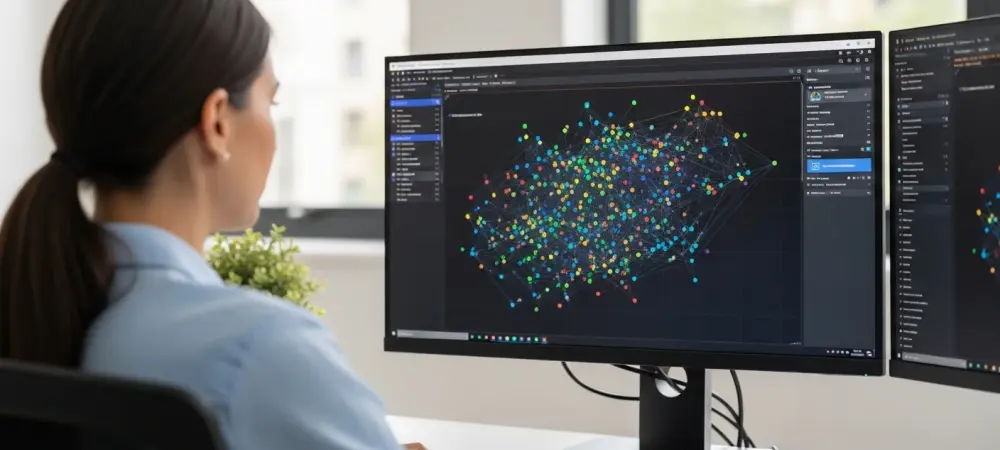
The relentless pace and sophistication of AI-augmented cyber threats have pushed traditional security operations to a breaking point, rendering purely reactive defense models increasingly obsolete and unsustainable. In this landscape, the strategic integration of high-fidelity threat intelligence has evolved from
- Cyber Security

The festive clamor of holiday greetings and year-end promotions provides the perfect cover for a sophisticated and rapidly evolving breed of cyber threat that capitalizes on seasonal distractions. While individuals and organizations are preoccupied with shopping, travel, and closing out
- Cyber Security

The very technologies celebrated for catapulting manufacturing into a new era of unprecedented efficiency are the same ones that have tragically made it the world’s most consistent target for cyberattacks. For years, the sector operated behind the perceived safety of
Browse Different Divisions
Popular Stories
Uncover What’s Next


















