Cyber Security
- Cyber Security

The rapid integration of Large Language Models into the modern enterprise stack has essentially redrawn the map of cyber warfare by exposing the fragile underpinnings of the software supply chain. While productivity gains have been undeniable, the rush to adopt
- Cyber Security

The rapid integration of Large Language Models into the modern enterprise stack has essentially redrawn the map of cyber warfare by exposing the fragile underpinnings of the software supply chain. While productivity gains have been undeniable, the rush to adopt
Popular Stories
- Cyber Security

A single, unsuspecting click on a seemingly routine password reset notification recently managed to dismantle a multi-billion-dollar retail empire in a matter of hours. This spear-phishing incident did not just leak data; it triggered a sophisticated ransomware wave that paralyzed
Deeper Sections Await
- Cyber Security
The seemingly harmless smart coffee maker in a kitchen or the networked thermostat on a wall can be weaponized into a soldier in a digital army, capable of launching massive cyberattacks that threaten critical national infrastructure. This escalating threat from
- Cyber Security

With a deep background in artificial intelligence and blockchain, Dominic Jainy has a unique perspective on the evolving landscape of digital threats. He has spent his career dissecting how complex systems can be exploited, making him an ideal voice to
Browse Different Divisions
- Cyber Security
The seemingly harmless smart coffee maker in a kitchen or the networked thermostat on a wall can be weaponized into a soldier in a digital army, capable of launching massive cyberattacks that threaten critical national infrastructure. This escalating threat from
- Cyber Security
The silent hum of servers now orchestrates corporate espionage with an autonomy that was pure science fiction just a few years ago, marking a definitive shift in the global cyber conflict. After years of theoretical discussions and experimental deployments, the
- Cyber Security

A hypothetical military operation in Venezuela, designed to capture President Nicolás Maduro, casts a stark light on the often-indistinguishable lines between conventional warfare and sophisticated cyber operations. This scenario, culminating in a mysterious blackout across Caracas, serves as a critical
- Cyber Security

From Digital Nuisance to Existential Threat Why 2026 Demands a New Security Paradigm What was once dismissed as a peripheral concern for IT departments has metastasized into a central business risk with the power to halt production lines, erase critical
- Cyber Security
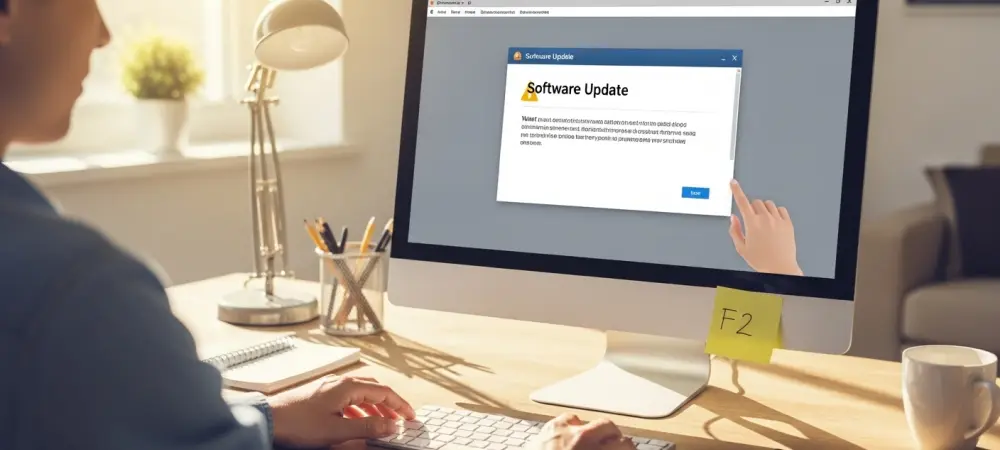
Understanding the Samsung Magician Vulnerability A critical security flaw discovered within a popular storage management application has shifted attention from typical virus threats to the utilities many users trust to optimize their systems. While Samsung security alerts typically prompt smartphone
- Cyber Security

With a deep background in artificial intelligence and blockchain, Dominic Jainy has a unique perspective on the evolving landscape of digital threats. He has spent his career dissecting how complex systems can be exploited, making him an ideal voice to
Browse Different Divisions
Popular Stories
Uncover What’s Next


















