Cyber Security
- Cyber Security

In the rapidly evolving world of cybersecurity, technical superiority is no longer the sole guarantor of success; the true battleground has shifted to commercial execution and market momentum. Dominic Jainy, an IT professional with deep roots in artificial intelligence, machine
- Cyber Security

In the rapidly evolving world of cybersecurity, technical superiority is no longer the sole guarantor of success; the true battleground has shifted to commercial execution and market momentum. Dominic Jainy, an IT professional with deep roots in artificial intelligence, machine
Popular Stories
- Cyber Security

A single, unsuspecting click on a seemingly routine password reset notification recently managed to dismantle a multi-billion-dollar retail empire in a matter of hours. This spear-phishing incident did not just leak data; it triggered a sophisticated ransomware wave that paralyzed
Deeper Sections Await
- Cyber Security

A seemingly moderate security flaw within a core Windows component has become the linchpin for sophisticated cyberattacks, forcing security teams globally into a race against adversaries who are already exploiting it in the wild. The first major security update of
- Cyber Security

Microsoft’s latest security bulletin has sent a clear and urgent message to system administrators worldwide, detailing a monumental update that addresses over one hundred vulnerabilities and casts a harsh spotlight on the persistent and evolving threats facing modern digital infrastructures.
Browse Different Divisions
- Cyber Security

A seemingly moderate security flaw within a core Windows component has become the linchpin for sophisticated cyberattacks, forcing security teams globally into a race against adversaries who are already exploiting it in the wild. The first major security update of
- Cyber Security

The fundamental equation of cybersecurity has been irrevocably altered, creating a critical and escalating disparity known as the “speed mismatch.” This concept defines the dangerous and widening gap between the operational tempo of sophisticated cyber adversaries and the validation cadence
- Cyber Security

While billions of users browse the web each day, a silent and relentless battle is waged within the very code that renders their favorite websites, a conflict that the latest Google Chrome 144 update brings into sharp focus. As an
- Cyber Security

Even with the widespread adoption of “end-to-end encryption” across major platforms, a critical vulnerability remains that federal agencies are urgently warning consumers about. Billions of messages traverse mobile networks daily, making them a high-value target for adversaries seeking personal, financial,
- Cyber Security
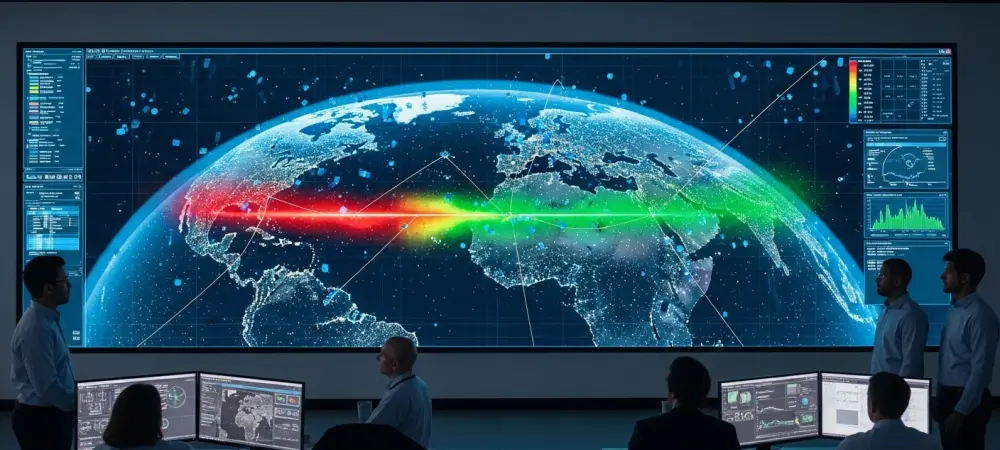
In the silent expanse above the Earth, a battle for information is being waged not with weapons, but with code, as a government’s attempt to enforce digital silence clashed with a global network designed to keep the world connected. This
- Cyber Security

Microsoft’s latest security bulletin has sent a clear and urgent message to system administrators worldwide, detailing a monumental update that addresses over one hundred vulnerabilities and casts a harsh spotlight on the persistent and evolving threats facing modern digital infrastructures.
Browse Different Divisions
Popular Stories
Uncover What’s Next
















