Cyber Security
- Cyber Security

In the rapidly evolving world of cybersecurity, technical superiority is no longer the sole guarantor of success; the true battleground has shifted to commercial execution and market momentum. Dominic Jainy, an IT professional with deep roots in artificial intelligence, machine
- Cyber Security

In the rapidly evolving world of cybersecurity, technical superiority is no longer the sole guarantor of success; the true battleground has shifted to commercial execution and market momentum. Dominic Jainy, an IT professional with deep roots in artificial intelligence, machine
Popular Stories
- Cyber Security

A single, unsuspecting click on a seemingly routine password reset notification recently managed to dismantle a multi-billion-dollar retail empire in a matter of hours. This spear-phishing incident did not just leak data; it triggered a sophisticated ransomware wave that paralyzed
Deeper Sections Await
- Cyber Security

The healthcare industry is confronting an unnerving new reality where cyberattacks are no longer just about stealing data but are increasingly engineered to intentionally dismantle the very operational capabilities that support patient care. A recent analysis reveals a staggering doubling
- Cyber Security
Today we’re joined by Dominic Jainy, a leading mind at the intersection of artificial intelligence and cybersecurity. We’ll be delving into the discovery of VoidLink, a sophisticated new malware framework targeting Linux and cloud systems, to understand what its advanced
Browse Different Divisions
- Cyber Security

The healthcare industry is confronting an unnerving new reality where cyberattacks are no longer just about stealing data but are increasingly engineered to intentionally dismantle the very operational capabilities that support patient care. A recent analysis reveals a staggering doubling
- Cyber Security
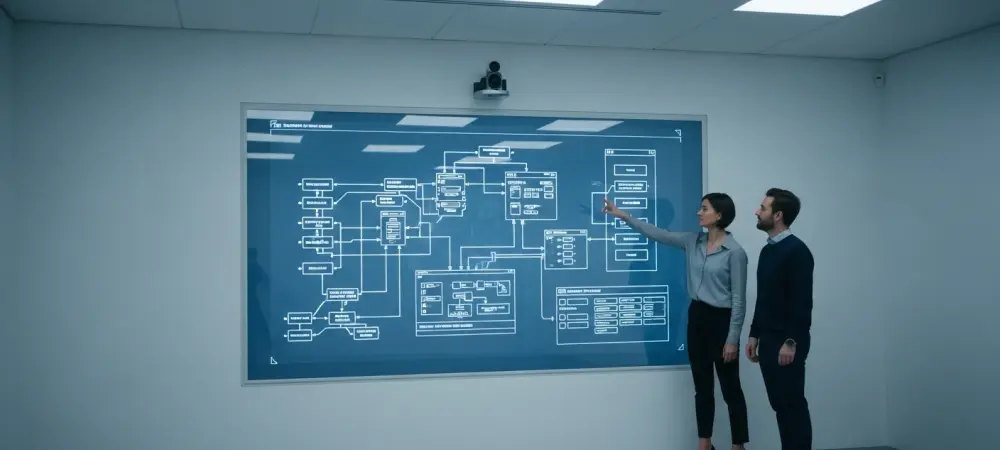
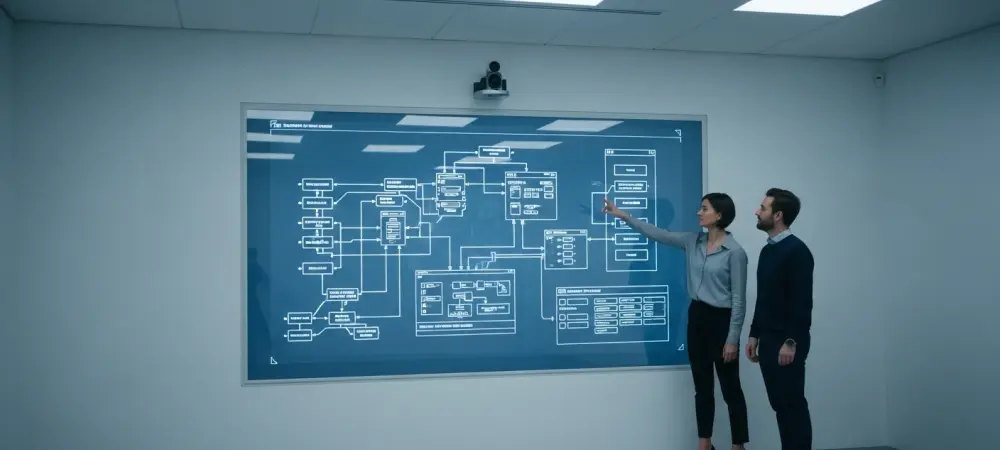
The sophisticated digital ecosystem, which is heavily reliant on artificial intelligence, interconnected devices, and pervasive automation, has fundamentally altered the landscape of cybersecurity, presenting an expanding attack surface that adversaries are exploiting with unprecedented speed and precision. The traditional boundaries
- Cyber Security

The silent, relentless hum of servers around the globe masks a precarious reality where the digital locks we trust to protect our most vital secrets are steadily becoming obsolete against threats that have already arrived. We are navigating a profound
- Cyber Security

We’re sitting down with Dominic Jainy, an IT professional with deep expertise in the digital landscape, to discuss a growing threat facing consumers. In the wake of major service disruptions, like the recent Verizon outage, a wave of sophisticated text-message
- Cyber Security

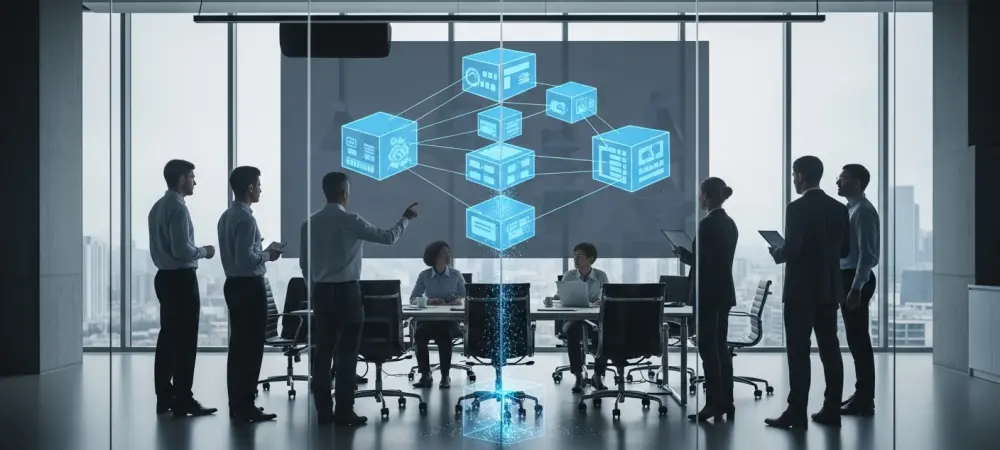
The very AI tools designed to streamline corporate operations and enhance productivity could have become the most devastating insider threat, wielded by an outsider with no credentials. This high-stakes scenario became a reality with the discovery of a critical vulnerability
- Cyber Security
Today we’re joined by Dominic Jainy, a leading mind at the intersection of artificial intelligence and cybersecurity. We’ll be delving into the discovery of VoidLink, a sophisticated new malware framework targeting Linux and cloud systems, to understand what its advanced
Browse Different Divisions
Popular Stories
Uncover What’s Next