The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has recently identified a critical security flaw in Adobe ColdFusion and added it to their Known Exploited Vulnerabilities (KEV) catalog. This flaw, cataloged as CVE-2023-26359, refers to a deserialization vulnerability found in Adobe ColdFusion 2018 and ColdFusion 2021. With a high CVSS score of 9.8, this vulnerability poses a significant risk by enabling arbitrary code execution without the need for user interaction. In this article, we will delve into the details of this flaw, its patch, exploitation concerns, and the urgency of applying necessary security updates.
Vulnerability Description
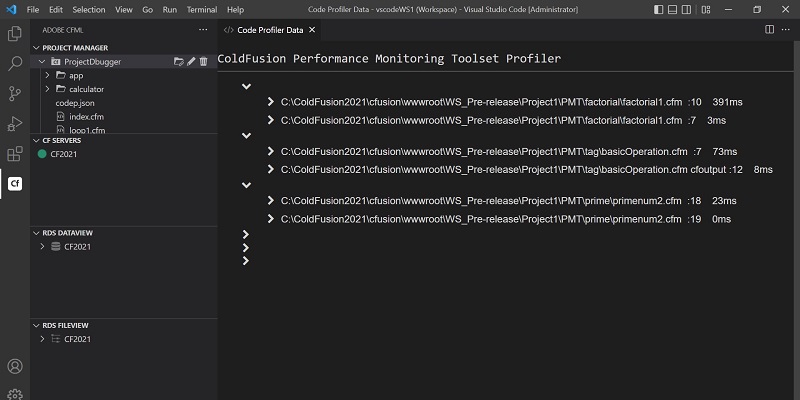
CVE-2023-26359 is a deserialization flaw present in Adobe ColdFusion 2018 and ColdFusion 2021. Deserialization, the process of converting data into a serialized format, can lead to code execution or denial-of-service if performed without proper validation or sanitization. In the case of this particular vulnerability, it allows an attacker to execute arbitrary code in the current user’s context without requiring any interaction. The severity of the flaw is evident from its high CVSS score, indicating the potential for significant exploitation and damage.
Recognizing the severity of the vulnerability, Adobe promptly addressed this flaw in March 2023 as part of their regular updates. By deploying these updates and implementing recommended security measures, users can effectively protect their systems against potential exploits. Adobe’s timely response and patch release highlight the importance of staying up-to-date with software updates to ensure a secure environment.
Exploitation Details
At this point, it remains unclear how exactly this vulnerability is being exploited in the wild. However, it is essential to note that this is not the first flaw impacting ColdFusion that has been added to CISA’s CVE catalog. Another flaw, identified as CVE-2023-26360, had previously been cataloged, indicating the continued importance of maintaining security measures and vigilant patch management in ColdFusion environments.
Limited Attacks and Urgency of Applying Security Updates
While the exact extent of exploitation is unknown, Adobe has reported “very limited attacks” exploiting the weakness in ColdFusion. This highlights the urgency for all organizations, particularly Federal Civilian Executive Branch (FCEB) agencies, to apply the necessary patches by September 11, 2023, in order to safeguard their networks from potential attacks. The significance of active exploitation serves as a reminder of the criticality of promptly implementing security updates and measures.
The inclusion of a critical security flaw in Adobe ColdFusion in CISA’s CVE catalog emphasizes the importance of proactively addressing vulnerabilities. CVE-2023-26359 poses a high risk due to its potential for arbitrary code execution without user interaction. Adobe acted swiftly to patch the flaw, but it is crucial for users and organizations to keep their systems updated and implement recommended security measures to ensure protection. The limited attacks reported by Adobe further underscore the necessity of applying security updates promptly, as the exploitation of vulnerabilities can have severe consequences. By remaining vigilant, applying patches, and prioritizing cybersecurity, users can fortify their systems against potential threats to their Adobe ColdFusion environments.