The shift from human-to-server traffic to machine-to-machine autonomy has finally hit a breaking point where traditional perimeter security is no longer just inefficient—it is an existential risk for the modern enterprise. Cloudflare Mesh arrived as a unified private networking fabric specifically designed to bridge this gap by addressing the needs of a world where software agents operate with increasing independence. Instead of relying on human-centric access models that assume a user is behind every request, this system creates a holistic environment that accommodates both people and autonomous code. By routing traffic through a high-performance global network, it ensures that every packet remains encrypted and entirely invisible to the public internet, effectively neutralizing common attack vectors before they can be exploited.
This transition reflects a strategic response to the rapid integration of artificial intelligence into daily business operations. Organizations have discovered that standard networking tools fail when forced to manage thousands of micro-interactions between AI agents and internal databases. Cloudflare Mesh provides the necessary infrastructure to govern these interactions without the latency penalties often associated with legacy security layers. It serves as the connective tissue for a decentralized workforce and a distributed machine labor force, prioritizing security without sacrificing the speed required for real-time computational tasks.
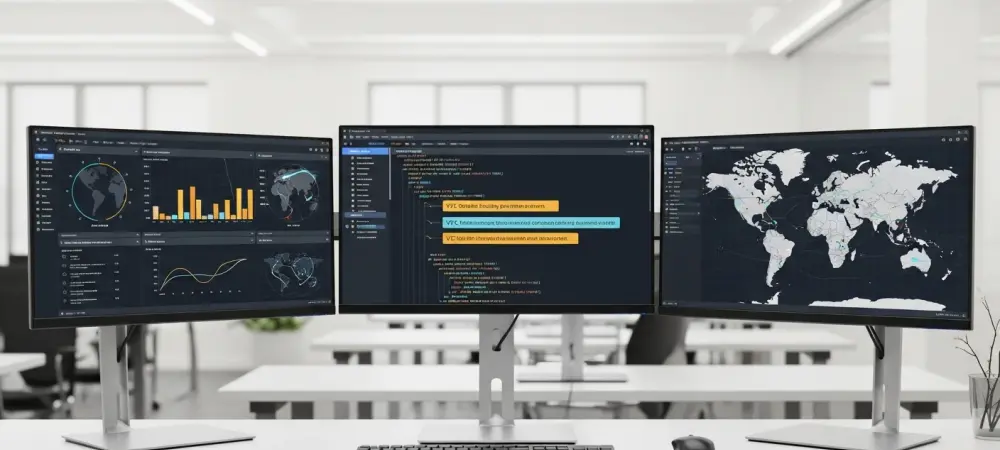
Architectural Components and Core Capabilities
Secure Private Interconnectivity: The Fabric of Modern Access
The fundamental strength of this mesh architecture lies in its ability to link human users, multi-cloud environments, and distributed edge devices into a single, cohesive network. Unlike traditional setups that require “clunky” and manual tunneling, this solution leverages a global Anycast network to reduce latency by bringing the entry point closer to the user or device. This approach replaces the need for legacy VPNs, which often become bottlenecks in high-traffic scenarios. By maintaining an encrypted path across diverse on-premise and cloud-based systems, the technology ensures that data remains protected even as it traverses potentially untrusted middle-mile infrastructure.
Moreover, the performance metrics indicate that this global routing strategy does more than just secure data; it optimizes it. By bypassing the unpredictable nature of the public internet, businesses can achieve more consistent throughput for their internal applications. This is particularly vital for companies operating across multiple regions, where the “middle mile” of the internet often introduces jitter and packet loss. The mesh effectively turns the global network into a private backplane, allowing for seamless connectivity that feels local despite the geographical distance between nodes.
Developer Integration: Connectivity as Code
The synergy between this networking fabric and the broader developer ecosystem marks a departure from hardware-heavy infrastructure management. Through the use of Cloudflare Workers and the Agents SDK, developers can now define networking parameters directly within their application code. This concept, known as Workers VPC bindings, allows for programmable access that adjusts dynamically based on the application’s needs. Instead of waiting for a network administrator to open a port or configure a firewall rule, a developer can specify connectivity requirements during the deployment phase, drastically shortening the development lifecycle.
In practice, this allows for granular control that was previously difficult to achieve without significant overhead. Teams can isolate staging environments from production systems with high precision, ensuring that an experimental AI model cannot inadvertently access sensitive customer data. By treating connectivity as a software-defined attribute, the mesh empowers engineering teams to build complex, distributed systems that are secure by default. This level of control is essential for maintaining agility in an environment where software updates are pushed dozens of times a day.
Agent Identity: Management of Digital Entities
One of the most innovative aspects of this technology is the conceptual shift toward treating AI agents as distinct identities with their own set of permissions. In traditional security models, automated scripts often ran under broad administrative accounts, creating a massive security hole if the script was compromised. Cloudflare Mesh implements a “least-privilege” model for every digital entity on the network. By assigning a specific identity to each agent, the system can enforce strict rules on what that agent can see and do, preventing lateral movement within the corporate network.
This identity-driven approach also simplifies the task of maintaining comprehensive audit trails. When an autonomous software agent makes a request, the system logs the action against that agent’s specific identity rather than a generic IP address or a shared service account. This transparency is crucial for compliance and troubleshooting, as it allows security teams to trace the exact path of a data request through the mesh. As AI agents take on more responsibility in data analysis and decision-making, the ability to govern their access with the same rigor as human employees becomes a non-negotiable requirement.
Trends and Innovations in AI-Driven Networking
The industry is currently witnessing a massive pivot toward AIOps, where the management of network traffic is increasingly handled by the very AI systems it supports. There is a growing necessity for operational layers that move beyond simple compute power to focus on secure data flow management. The trend is moving away from simply “connecting things” toward “governing interactions.” This shift is driven by the realization that as AI models become more complex, the risk of data leakage or unauthorized access grows exponentially.
Furthermore, there is a clear movement toward eliminating any public internet exposure for private APIs and internal databases. Modern enterprises are realizing that a “dark” network—one that cannot be scanned or targeted from the outside—is the only way to achieve true resilience. This innovation allows companies to leverage the power of the cloud while maintaining the security of an air-gapped system. As this trend matures, the distinction between internal and external networks will continue to blur, replaced by a single, identity-verified fabric.
Real-World Applications and Use Cases
In corporate environments, this technology has been deployed to facilitate secure AI coding assistants that need access to internal repositories without exposing that code to external threats. By placing the coding assistant within the mesh, developers can benefit from AI-powered suggestions while ensuring that their proprietary logic remains within the company’s protected perimeter. Similarly, financial institutions are using these private fabrics to run internal data analysis tools that process sensitive transaction records, keeping the data flow entirely within an encrypted and audited environment.
Software development houses have also found significant value in sandboxing autonomous agents. During the testing phase, these agents can be granted limited access to specific datasets to verify their functionality without risking the integrity of the broader network. This capability is particularly useful in sectors like technology and finance, where protecting the “crown jewels”—such as source code or customer financial data—is paramount. Notable implementations have shown that this approach reduces the time required to move from AI trial to full production by providing a pre-secured environment for deployment.
Challenges and Technical Limitations
Despite the benefits, migrating legacy infrastructure into a modern mesh architecture remains a significant hurdle for many organizations. Older systems often rely on hardcoded IP addresses or legacy protocols that do not easily translate to a software-defined, identity-driven environment. This creates a technical debt that must be addressed before the full advantages of the mesh can be realized. Additionally, regulatory and compliance issues regarding data residency can complicate deployments, as different jurisdictions have varying rules on how and where data can be routed, even if it is encrypted.
Market obstacles also exist regarding the speed of enterprise adoption. While the technology is ready for large-scale use, many organizations are still caught in the transition from AI experimentation to production. Scaling a mesh network to handle massive deployments of autonomous agents requires a level of coordination between IT, security, and development teams that is not always present. Ongoing efforts to refine the scalability of these networks continue, but the human element of organizational change often remains the slowest part of the process.
Future Outlook and Strategic Evolution
The trajectory of identity-driven networking suggests a future where the enterprise network is completely abstracted from the physical location of its components. Cloudflare Mesh is positioned to become the default bridge between diverse cloud providers like AWS and Google Cloud and private data centers. This multi-cloud interoperability will allow businesses to avoid vendor lock-in, moving their workloads to whichever provider offers the best price or performance while maintaining a consistent security posture across the entire estate.
Looking ahead, the convergence of human and machine access will likely redefine the concept of a “corporate network” entirely. We can expect breakthroughs in how identity is verified, perhaps moving toward continuous authentication models where the behavior of an agent or user is constantly monitored for anomalies. This evolution will make the network more resilient and more responsive to threats. The goal is to create a self-healing fabric that automatically isolates compromised nodes while maintaining uninterrupted service for the rest of the organization.
Conclusion and Assessment
The development of Cloudflare Mesh marked a significant milestone in the effort to modernize private networking for the autonomous age. By providing a rapid, encrypted fabric that replaced slow and cumbersome legacy systems, the technology offered a viable path forward for enterprises struggling with the security implications of AI. The performance metrics demonstrated that a global network could effectively serve as a private backplane, delivering both speed and invisibility to sensitive assets. This shift validated the idea that identity, rather than location, should be the primary factor in determining network access.
The implementation of these systems showed that the most successful organizations were those that treated networking as a programmable resource. The integration with developer tools simplified the deployment of secure AI agents and allowed for a level of granular control that was previously unattainable. As businesses continue to integrate autonomous digital entities into their core workflows, the lessons learned from this transition highlighted the necessity of a unified networking fabric. The strategic evolution of this technology established a new standard for secure operations, ensuring that the enterprise network remained a facilitator of innovation rather than a bottleneck.