A high-stakes digital heist in the modern era rarely begins with a broken firewall or a brute-force entry; instead, it starts with a friendly LinkedIn message from a seemingly reputable venture capitalist. This is the hallmark of the ClickFix campaign, a highly coordinated operation that emerged in early 2026 to systematically target high-value individuals within the cryptocurrency, decentralized finance, and Web3 sectors. Unlike broad phishing attempts that rely on volume, this threat is a surgical strike designed to exploit the professional curiosity of developers and executives. The significance of the ClickFix operation lies in its seamless integration of psychological manipulation and technical stealth. By focusing on the very individuals who build and manage the world’s digital assets, the attackers have identified a lucrative niche where one successful compromise can lead to the loss of millions in capital. It represents a paradigm shift where the social interaction itself is the primary vulnerability, turning the standard professional networking process into a dangerous gauntlet for modern professionals.
Origins and Context of the ClickFix Operation
The ClickFix campaign first came to light in early 2026 after security researchers noticed a surge in targeted attacks against blockchain startups. Its roots are firmly planted in the evolution of cyber-espionage tactics, moving away from simple malware attachments toward sophisticated, multi-layered interactions. This operation did not appear in a vacuum; it utilized established infrastructure and refined methods that have been observed in previous high-level crypto-sector breaches.
The credibility of this threat is bolstered by its connection to a network of back-end servers and domains that mimic legitimate corporate environments. This historical precedent in the crypto industry shows that attackers are no longer content with random targets. They now build entire ecosystems of deception, including fake news outlets and investment platforms, to ensure that their eventual malware delivery feels like a natural step in a legitimate business conversation.
Key Tactics: The Multi-Staged Attack Vector
At its core, the ClickFix operation is defined by a multi-staged approach that prioritizes the circumvention of traditional security perimeters. The attackers recognized that modern endpoint protection is quite effective at stopping unsolicited downloads. Consequently, they designed a system where the victim is guided through a series of “verification” steps, each one appearing more legitimate than the last, until the user eventually executes the malicious code themselves.
These technical milestones are significant because they rely on user-initiated actions that often bypass the behavioral analysis of security software. By leading the victim through a logical progression of professional interactions—starting from social media and moving to a simulated technical environment—the campaign achieves a level of persistence that standard malware struggles to maintain. This approach effectively turns the user into an unwitting accomplice in their own system’s compromise.
Fabricated Corporate Identities and Social Engineering
The campaign relies heavily on the “Mykhailo Hureiev” persona, a meticulously crafted identity presented as a co-founder of the fictitious SolidBit Capital. This persona is used to reach out to targets on LinkedIn with offers of partnership or investment. The social engineering is not limited to messages; the attackers created an entire constellation of fake firms like MegaBit and Lumax Capital to provide a veneer of professional history and success.
To build trust, these firms feature polished websites and professional headshots, many of which appear to be AI-generated to avoid detection through reverse image searches. When a target receives a message from Hureiev, they find a well-documented professional profile that mirrors the standards of the venture capital world. This “fake venture capital” tactic is specifically designed to lower the defenses of entrepreneurs who are constantly seeking new funding and strategic partnerships.
The Innovative ClickFix Delivery Mechanism
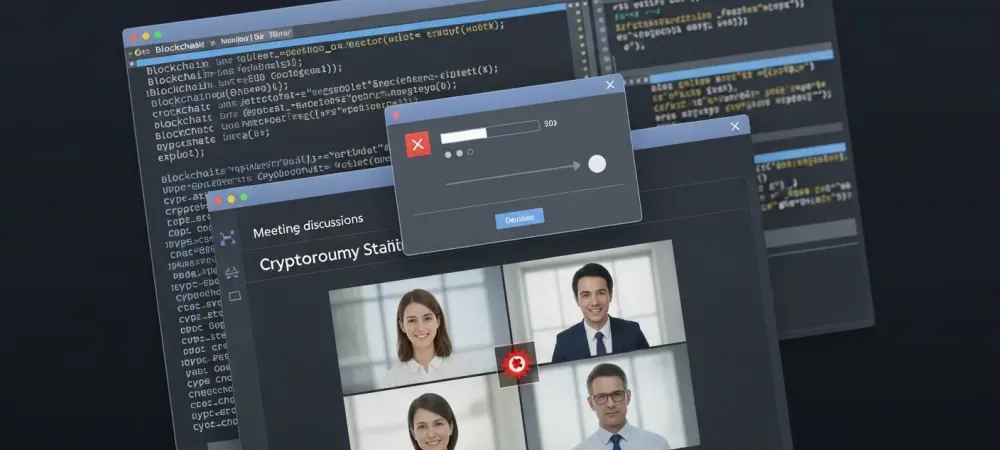
Once a rapport is established, the victim is invited to a virtual meeting on what appears to be a standard conferencing platform. However, the link leads to a spoofed page designed to look like Zoom or Google Meet, often branded with the logos of legitimate industry events like “The Digital Asset Conference.” Upon arrival, the user is greeted with a fraudulent Cloudflare verification box, a familiar sight that adds a false sense of security and technical legitimacy. The innovation here is the way the CAPTCHA interaction functions. When a user interacts with the verification box, the site identifies the visitor’s operating system and silently injects a malicious command into their clipboard. The victim is then prompted to paste a “verification code” into their terminal or PowerShell window to gain access to the meeting. This clever manipulation uses a common technical workflow to deliver the infection without any traditional file download occurring.
Cross-Platform Execution Strategies
The ClickFix campaign demonstrates a high level of technical versatility by employing different execution strategies for various operating systems. For Windows users, the clipboard command triggers a PowerShell script that runs entirely in memory. This memory-based execution is particularly dangerous because it leaves no trace on the hard drive, making it nearly impossible for traditional antivirus programs to detect the presence of the malware through standard file scanning.
In contrast, the campaign targets the large population of crypto developers who use macOS with a persistent Python-based approach. The bash command provided to Mac users ensures that Python 3 is installed and then downloads a script from a remote command-and-control server. This script is designed for long-term residency, allowing the attackers to maintain access to the device, monitor activity, and eventually exfiltrate private keys or other sensitive credentials related to digital asset management.
Distinguishing Characteristics of the Campaign
What sets ClickFix apart from standard phishing is its aggressive “living-off-the-land” methodology. Instead of introducing a new, suspicious file to the system, it uses the computer’s own built-in tools, like PowerShell and Bash, to carry out the attack. This approach is highly effective because these tools are essential for the daily work of developers and IT professionals, meaning they are rarely blocked by corporate execution policies.
Moreover, the campaign utilizes heavy obfuscation and incredibly “lean” binaries. One version of the malware was found to be packed with garbage code to frustrate automated analysis, while another version was so stripped down that it achieved a zero-detection rate on major scanning platforms. This dual strategy of being either too complex to understand or too small to notice ensures that the infection remains undetected for as long as possible.
Current Threat Landscape and Attribution
The infrastructure supporting this campaign has been traced back to registrations linked to an individual named Anatolli Bigdasch, purportedly based in Boston. While the name may be a pseudonym, the monitoring of the associated command-and-control servers shows a persistent and active operation. These servers act as the central nervous system for the malware, receiving stolen data and pushing new commands to compromised devices across the globe. Analysts have noted strong operational links between ClickFix and the group known as UNC1069. This group has suspected ties to North Korean state-sponsored activity and has been a constant presence in the crypto-threat landscape for several years. The focus on high-value digital asset targets and the use of complex social engineering personas are hallmarks of these state-sponsored actors, who view the crypto sector as a primary source of illicit revenue.
Reflection: Broader Impacts
The success of the ClickFix campaign forces a difficult reflection on the nature of digital trust. It highlights that technical defenses are only as strong as the human processes they support. By exploiting the necessity of virtual networking and the commonality of technical troubleshooting, the attackers have turned standard professional behaviors into high-risk activities. This forces a re-evaluation of how teams interact in a remote-first world. This campaign will likely necessitate a shift toward “Zero Trust” interactions even in casual professional networking. The days of clicking meeting links or running verification scripts without extreme scrutiny are effectively over for those in high-stakes industries. This shift will fundamentally alter professional workflows, making the process of building new connections more cumbersome but significantly more secure as the blockchain community adapts to these persistent threats.
Summary: ClickFix Threat and Preventative Measures
The ClickFix campaign established a new benchmark for sophisticated social engineering within the financial technology sector. Organizations found that their primary defense rested not on software updates alone, but on the rigorous training of their personnel to recognize the subtle signs of a coordinated persona-based attack. This operation demonstrated that as long as humans remained the gatekeepers of digital keys, they would remain the primary focus of state-sponsored actors.
To safeguard the future of the crypto sector, professionals adopted stricter security protocols, such as the mandatory use of URL scanners for all meeting invitations and the implementation of terminal-pasting restrictions. Security teams emphasized that no legitimate conferencing platform would ever require a user to execute a PowerShell or Bash script to join a call. These preventative measures, combined with a heightened awareness of domain registration age and persona verification, formed the backbone of a more resilient digital asset ecosystem.