Dominic Jainy has spent years at the crossroads of AI, cloud security, and data platforms, helping teams translate complex architectures into resilient, testable recovery plans. In this conversation, we explore how to protect BigQuery, Compute Engine, GKE, Cloud SQL, and Google Workspace with a single operating model on Google Cloud. We cover threat scanning that doesn’t bust backup windows, isolation patterns that blunt ransomware and insider risks, and automated policy recommendations that raise coverage without drowning teams in alerts. We also dig into marketplaces, governance, FinOps, and why 55% of organizations still feel shaky about recovery—and what to do about it.
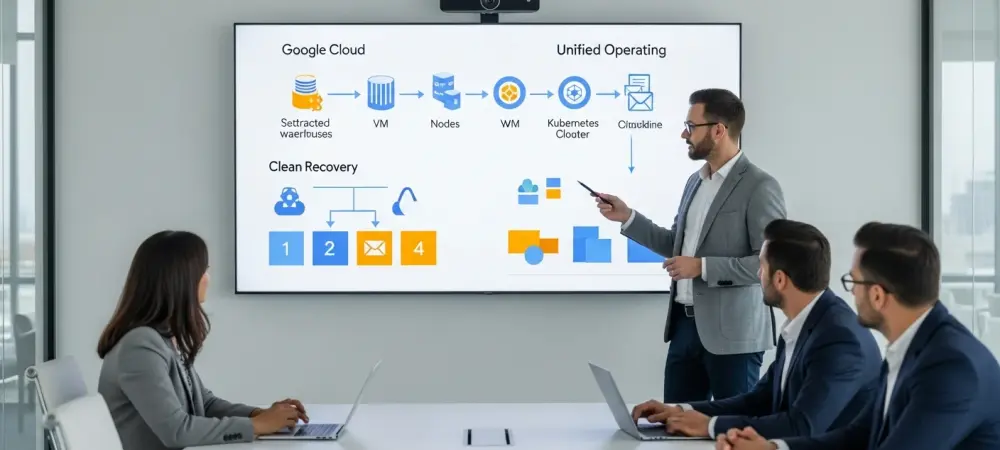
Many teams run BigQuery, Compute Engine, GKE, Cloud SQL, and Google Workspace together. How would you prioritize protection across these services, and what step-by-step runbook would you use to test recovery? Please share specific RTO/RPO targets and any hard lessons from past incidents.
I tier by blast radius and change velocity: Cloud SQL and GKE stateful sets get top priority, then Workspace for continuity, then Compute Engine and BigQuery by data criticality. My runbook is simple: declare incident scope, freeze change, pick the clean recovery point, restore metadata first, then data, then access, and finally validate with app owners. I test quarterly with service-level drills, always including at least one cross-project and one cross-region scenario to surface IAM and network drift. The hard lesson was skipping metadata; we once restored data fast but missed permissions and CRDs, and the clocks kept ticking while users still couldn’t work, a reminder that recovery confidence matters because 55% still doubt they can bounce back.
Threat scanning for backups promises early malware detection. How do you prevent scanning from delaying backup windows, and what thresholds or indicators trigger quarantine? Walk us through one real incident where scanning changed the recovery plan and the metrics that proved its value.
I offload scanning to a sidecar pipeline, using snapshot-then-scan so protection points finish first and scanning runs asynchronously. Quarantine triggers when multiple signals converge: anomalous encryption patterns, sudden file entropy spikes, and policy-violating executables in known-clean directories. In one incident, scanning flagged suspect deltas across a narrow time band, so we rolled back to the prior point-in-time set and skipped contaminated slices. The value showed up in fewer rework cycles and faster cutover, and it strengthened executive conviction in cyber recovery when set against that 55% confidence gap.
Isolated backup storage aims to resist ransomware and insider threats. What isolation patterns (air gap, immutability, role separation) do you recommend on Google Cloud, and how do you test them? Include access workflows, break-glass procedures, and audit metrics you track.
I pair logical air gaps with immutability and strict role separation so production credentials can’t reach vaulted copies. Access flows through a request in a secured channel, just-in-time elevation, and time-bound tokens, with break-glass guarded by multi-approver workflow and immediate SOC notification. Tests simulate credential theft and lateral movement, proving that deletes are blocked and immutability windows hold. I track denied-delete counts, unauthorized access attempts, and every break-glass use, then review drift in quarterly rounds because resilience fails quietly before it fails loudly.
Automated policy recommendations based on workload classification sound powerful. How do you classify diverse workloads at scale, and what misclassification pitfalls have you seen? Please outline a step-by-step tuning process and a concrete before/after snapshot of coverage metrics.
I start with discovery, tag ingestion, and pattern matching on service type, data sensitivity, and change rate, then let the platform suggest policies. Pitfalls include overfitting dev labels to prod clones and missing transient data in ephemeral namespaces. Tuning means sampling false positives and negatives weekly, refining tags, and hardening overrides for crown jewels. After runs, I expect visibly higher protected-to-under-protected ratios and fewer orphaned assets, a demonstrable shift in the direction that 55% want to see to trust fast recovery.
Some organizations discover unprotected or under-protected cloud resources late. How do you continuously surface protection gaps across projects and regions, and what governance model closes them? Share the dashboards, alert thresholds, and escalation paths that actually work.
I use continuous discovery to inventory resources daily and map each to a policy baseline, with exceptions highlighted by age and criticality. Dashboards show unprotected assets by project and region, rising trend lines, and SLA variance. Alerts fire on first sight for high-risk workloads and on sustained duration for low-risk ones, with a clear handoff from app teams to a central platform squad. Escalation jumps to leadership when a gap persists, because lingering risk is exactly why 55% still lack confidence.
Gmail and Google Drive backups have unique challenges. How do you handle versioning, legal holds, and rapid user-level restores without disrupting live workflows? Offer a step-by-step playbook for a department-wide restore and the KPIs you’d monitor.
I preserve versions with immutable retention and apply legal holds as policy objects, not ad hoc rules. For a department restore: scope identities, choose the clean recovery point, restore to side mailboxes and drives, run spot checks, then promote and notify. I keep end-user friction low by avoiding in-place overwrites until validation passes. KPIs include restore throughput, error rates, and time from request to user access, and I compare those trends against that 55% benchmark for confidence uplift.
GKE introduces stateful workloads, operators, and CRDs. How do you achieve app-consistent backups for Kubernetes, and what’s your approach to secrets, PersistentVolumes, and multi-namespace restores? Please include a real migration or failover story with timings and pitfalls.
I capture the entire app graph—namespaces, CRDs, RBAC, and PVs—in a single consistent point so dependencies rehydrate together. Secrets ride through sealed storage or are reissued from a managed vault during restore, while PV snapshots align with pre-freeze and post-thaw hooks. For multi-namespace work, I restore into a staging cluster first to validate controllers and admission policies. A migration taught us to export operator CRDs before data movement; skipping that step left pods stuck pending and dragged out the cutover longer than anyone wanted, exposing why 55% feel uneasy.
Credit-based pricing through a cloud marketplace can simplify procurement. How should teams forecast credits versus usage, and what FinOps practices avoid surprise bills? Share examples tying backup frequency, retention, dedupe, and egress to spend, with concrete numbers.
I map credit forecasts to protection patterns: snapshot cadence, retention tiers, and expected change rates, then adjust monthly with real consumption. FinOps practices include tagging by app and environment, commitment alignment with seasonality, and right-sizing immutability windows. Dedupe policies must track workload volatility so credit burn reflects real data churn, not habits. Egress stays low when restores land in-region, which becomes a standard unless cross-cloud mandates apply for the minority that need it, an issue intertwined with the 55% confidence theme.
Many leaders admit low confidence in rapid cyber recovery. What sequence of tabletop exercises and live-fire drills most improves confidence, and how do you measure progress? Include cadence, tooling, and the specific metrics that convince executives.
I run monthly tabletops, then quarterly live-fire restores that include malware-tainted restore points and force clean-point selection. Tooling ties backup telemetry to incident response so the story from alert to restore is traceable and fast. Executives respond to reduced time from detection to validated recovery and a declining count of blocked restores due to access or policy drift. The goal is to move leadership out of that 55% uncertainty and into fact-based confidence.
AI-driven operations are accelerating change. Where can AI help in anomaly detection, policy generation, and triage without flooding teams with noise? Describe a case where AI reduced time-to-detect or time-to-recover, including precision/recall trade-offs.
AI helps most when signals are fused: data entropy, IAM anomalies, and workload drift informing a single ranked incident card. Policy generation works when AI proposes baseline templates and humans certify exceptions, keeping false positives under control. In practice, AI flagged a narrow window of risky deltas, so we chose a prior restore point sooner and trimmed back-and-forth with app owners. The qualitative win was fewer noisy alerts and clearer action, a step toward shrinking that 55% doubt.
Cloud marketplaces align security buying with existing commitments. How does that change deployment timelines, stakeholder alignment, and post-purchase enablement? Please walk through a day-by-day onboarding plan from purchase to first successful recovery.
Marketplace routes collapse procurement friction and align budgets with platform roadmaps, so security, ops, and finance start on the same page. Day 1 is purchase and identity setup; Day 2 is project onboarding and least-privilege roles; Day 3 is discovery and baseline policies; Day 4 is first backup; Day 5 is first restore test. Post-purchase enablement pairs a platform owner with app leads to codify runbooks and acceptance tests. Hitting that first success fast builds trust where 55% still hesitate.
Integrating with native Google services can streamline ops. How do you connect with Security Command Center, Chronicle, IAM, CMEK, and VPC Service Controls? Provide exact integration steps, least-privilege IAM roles, and key telemetry you feed back to SOC workflows.
I enable SCC findings ingestion, forward backup and scan events to Chronicle, and lock encryption with CMEK so keys stay customer-controlled. IAM follows least privilege: separate roles for discovery, backup execution, and vault administration, each time-bound and monitored. VPC Service Controls fence data exfil, and service perimeters are validated during restore drills. Telemetry to SOC includes attempted delete events, quarantine actions, and restore approvals, closing the loop from signal to recovery decision.
Data residency, egress costs, and cross-cloud recovery introduce trade-offs. How do you balance geo-redundancy with compliance and cost, and when is multi-cloud recovery worth it? Share a decision matrix and a real cost breakdown for one failover scenario.
I decide with three axes: regulatory residency, business impact of downtime, and data mobility constraints. If residency is strict, I keep copies within allowed regions and validate restores there first, adding cross-region only where policy permits. Multi-cloud recovery is reserved for workloads whose dependency chains can tolerate differing controls and where sovereignty or procurement demands it. Confidence rises when choices are explicit and auditable, again addressing that 55% recovery concern.
Insider threats remain a concern. What controls prevent malicious deletion or policy tampering, and how do you verify them? Describe role design, approval workflows, and quarterly control testing with sample results that proved resilience.
I enforce dual control for destructive actions, immutable retention, and continuous config drift detection. Roles split duties: no one can both set policy and execute deletion, and changes require multi-party approvals. Quarterly tests attempt policy tampering and force-delete scenarios to prove blocks, with all results reviewed by risk and security. Each cycle that shows denied actions and intact immutability strengthens confidence in a world where 55% still worry.
What is your forecast for cloud cyber resilience?
Resilience will become a default operating feature, not a niche add-on, as marketplaces and native integrations make adoption routine. AI will help close the detection-to-recovery gap, but human-approved policies and immutable design will remain the safety rails. Cross-cloud capabilities will persist, yet most wins will come from disciplined, automated recovery inside a single platform with smart isolation and scanning. If teams practice relentlessly and measure progress, that 55% will shrink, and recovery will feel less like a gamble and more like muscle memory.