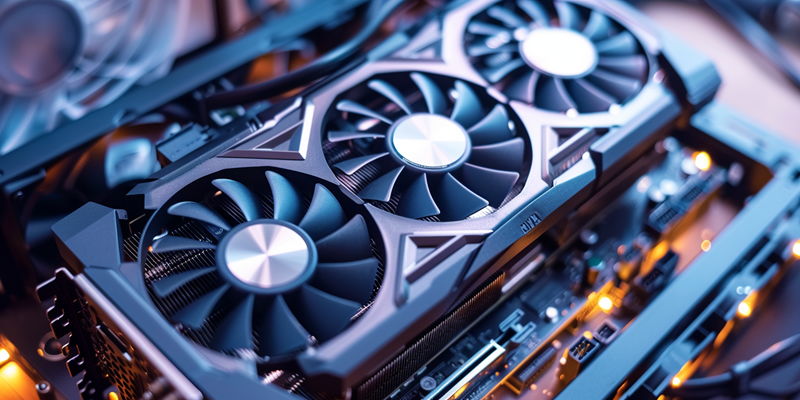
Shanghai Pudong International Airport recently seized 44 used GPUs disguised as new ones, highlighting China’s ongoing fight against tech smuggling. Smugglers often attempt to avoid taxes and regulations, making the smuggling of CPUs and GPUs a consistent issue. Despite tough customs enforcement, smugglers resort to increasingly creative methods to circumvent the law, thereby challenging the effectiveness of China’s current strategies. The high profits from the black market, driven by strong demand and price differences due to taxes and import duties, entice smugglers. China’s crackdown extends beyond airports, with actions at various entry points. However, these efforts still struggle against the smarts of smugglers who use advanced tech and global networks to elude detection. This incident underscores the need for continuous revision of anti-smuggling measures to stay ahead of innovative illegal trading tactics.
The Counter-Smuggling Strategy
Chinese officials are consistently cracking down on smuggling rings, showcased by recent significant seizures like the GPUs at Shanghai airport. These efforts illustrate China’s strong enforcement against an ongoing tide of illegal electronic goods trade. While advanced scans and strategic intelligence are instrumental, the resilient black market for electronics demands more comprehensive methods.
Experts advocate for a multifaceted offensive, encompassing better international collaboration, stronger legal systems, and tackling the demand side. Addressing China’s internal demand could potentially weaken smuggler networks; public awareness campaigns and incentives for authentic goods, along with bolstering domestic industries, could reduce reliance on illicit channels. This approach, alongside China’s continued enforcement vigor, holds the key to counteracting the persistent GPU smuggling challenge.