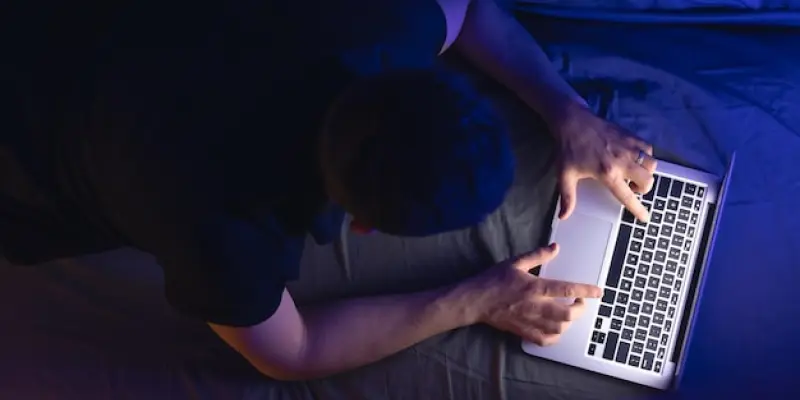
In the world of entertainment, convenience and access to digital content have reshaped how audiences consume media, but the allure of pirated streaming poses severe security risks. Cybercriminals are increasingly exploiting the enthusiasm for popular movies and TV series by embedding malicious software and phishing schemes into unauthorized digital content. This tactic targets unsuspecting viewers seeking early access to unreleased entertainment, luring them into a web of deceit that can result in significant cyber threats. The dangers extend beyond individual users, putting both personal and organizational data at risk. As digital consumption continues to surge, understanding the severity of these threats and the importance of staying vigilant becomes vital. The adoption of safe practices and reliance on legitimate streaming services is paramount for maintaining security.
Insights from Industry Leaders
Experts in cybersecurity are sounding alarms about the sophisticated methods employed by cyber attackers in the realm of pirated streaming platforms. Companies like Kaspersky and Microsoft have observed an escalating trend where cybercriminals leverage these illegal services to conduct widespread security breaches. These perpetrators mask malicious intents within alluring content—often using fake login pages and malware-ridden downloads to collect sensitive information, such as passwords and financial details. Cybersecurity professionals emphasize the significance of recognizing fake pages and understanding that simply clicking on a seemingly harmless link can lead to devastating outcomes. Users are encouraged to ensure that downloaded content adheres to standard video file extensions, thereby minimizing exposure to hidden threats. The insights delineated by these industry leaders underscore a common goal—enhancing user awareness and protection against the ever-evolving tactics of cybercriminals.
Strategies for Safe Digital Consumption
In the ongoing battle against cyber threats linked to pirated content, the push for utilizing reputable streaming services has never been more vital. These platforms allocate resources to security measures that safeguard user data, ensuring a secure environment for digital consumption. By opting for paid subscriptions, users support content creators and receive quality assurances, along with peace of mind. Contrarily, pirated services, though seemingly appealing, compromise user security, making them vulnerable to malware, identity theft, and data breaches. Cybersecurity experts emphasize that the allure of pirated content pales in comparison to the significant risks it carries. Increasing public awareness and education are key themes in addressing cyberattacks in this realm. As consumers continue to turn to online entertainment, adopting responsible behaviors and sticking to reputable sources will protect against the sophisticated traps set by cybercriminals. Recognizing these risks and choosing legitimate services can help users avoid potential cyber threats, ensuring a safe digital experience.