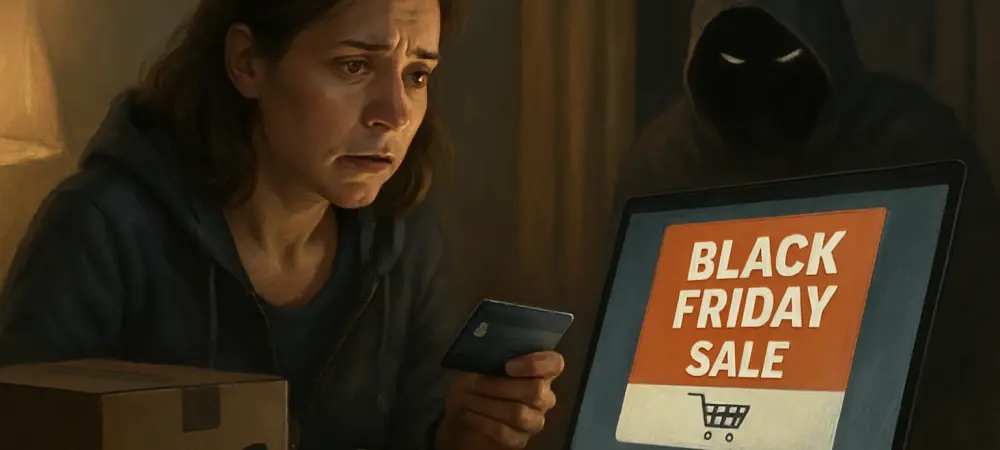
Imagine eagerly awaiting a Black Friday deal from Amazon, only to click on an email promising a steep discount and find yourself locked out of your account, your personal data stolen. This nightmare scenario is becoming all too common as cybercriminals ramp up their efforts during the holiday shopping frenzy. With over 310 million active users, Amazon stands as a prime target for phishing scams, especially during high-traffic events like Black Friday. This guide aims to equip Amazon shoppers with the knowledge and tools needed to identify and avoid these sophisticated scams, ensuring a safe and secure shopping experience.
The importance of staying vigilant cannot be overstated during this season of heightened online activity. Scammers exploit the excitement and urgency surrounding holiday deals, crafting convincing traps that can deceive even the most cautious users. By following the practical steps outlined here, shoppers can protect their sensitive information from falling into the wrong hands. The surge in cyber threats, particularly those driven by advanced technology, underscores the need for awareness and proactive measures to safeguard personal and financial security.
Why Amazon Shoppers Are Vulnerable During Black Friday
The sheer scale of Amazon’s user base makes it an irresistible target for cybercriminals looking to exploit trusting customers. During Black Friday, when millions are hunting for deals and expecting frequent shipping updates, the opportunity for deception multiplies. Scammers know that shoppers are more likely to act quickly on a limited-time offer or respond to a delivery notification without scrutinizing the details, creating a perfect storm for fraud. Moreover, reports from cybersecurity experts reveal a staggering 620% increase in phishing attacks during November, with Amazon accounting for 80% of brand impersonation scams. This statistic highlights how fraudsters prioritize mimicking Amazon over other major brands due to its massive reach and the inherent trust users place in its communications. The holiday rush amplifies this vulnerability, as the anticipation of bargains clouds judgment and lowers defenses against suspicious messages.
Beyond the numbers, the emotional pull of the season plays a significant role in making users susceptible. The desire to snag a deal or ensure a gift arrives on time can override the instinct to double-check an email sender or website link. Understanding this dynamic is the first step toward building a stronger shield against these pervasive threats that lurk behind seemingly innocent notifications.
Step-by-Step Guide to Protect Yourself from Phishing Scams
Step 1: Recognize the Signs of a Phishing Attempt
The first line of defense against phishing scams lies in spotting the warning signs before taking any action. Scammers often send emails or texts that mimic Amazon’s branding, claiming to offer exclusive deals or urgent shipping updates. These messages might urge immediate clicks on links that lead to counterfeit websites designed to steal login credentials or payment information. Pay close attention to subtle discrepancies, such as odd email addresses or URLs that don’t match Amazon’s official domain.
Additionally, look for red flags like grammatical errors or awkward phrasing, which can betray a scam despite polished visuals. Fraudsters rely on the holiday bustle to distract users from noticing these small but telling mistakes. Taking a moment to inspect the sender’s details and hover over links without clicking can prevent falling into a trap set with deceptive precision during peak shopping times.
Step 2: Avoid Falling for Holiday-Themed Bait
During Black Friday, the expectation of deals and delivery confirmations makes shoppers particularly vulnerable to tailored phishing attempts. Scammers exploit this by crafting messages that play on the urgency of limited-time offers or the anxiety of delayed packages. Resisting the impulse to act on these prompts without verification is crucial, as haste often leads to costly errors in judgment. A practical tip is to navigate directly to Amazon’s official website or app for any updates rather than clicking on links provided in unsolicited messages. This simple habit bypasses the risk of landing on a fake page that looks eerily similar to the real thing. Staying grounded amidst the holiday excitement helps maintain a clear perspective, ensuring that no deal, no matter how tempting, compromises security.
Step 3: Leverage Security Features for Added Protection
Enhancing account security with available tools offers a robust barrier against phishing threats. Enabling two-factor authentication on an Amazon account ensures that even if a password is compromised, an additional verification step prevents unauthorized access. Incorporating passkeys, where supported, adds another layer of defense by replacing traditional passwords with more secure alternatives.
Beyond these settings, regularly monitoring account activity for unfamiliar logins or purchases can catch potential breaches early. Amazon provides clear guidelines on securing accounts, and adhering to these recommendations fortifies personal defenses against increasingly sophisticated attacks. Proactively adopting these measures transforms a potential target into a fortified user, less appealing to cybercriminals seeking easy prey.
Step 4: Be Wary of AI-Driven Personalization in Scams
The rise of artificial intelligence has armed scammers with tools to create hyper-personalized phishing attempts at alarming speeds. Using data from breaches or social media, attackers can tailor emails that reference past purchases or personal details, making them seem legitimate. Awareness of this technological edge is essential, as these messages often bypass initial skepticism with their uncanny accuracy.
Furthermore, emerging agentic AI can adapt phishing campaigns in real-time, evading traditional security filters with machine-driven precision. Staying cautious of any communication that seems overly specific or urgent, even if it appears personalized, helps counter this evolving threat. Relying on direct interaction with Amazon’s platforms rather than external prompts remains a key strategy in outsmarting these high-tech deceptions.
Step 5: Understand the Consequences and Act Swiftly if Tricked
If a phishing scam succeeds, the fallout can include identity theft, financial loss, or even further exploitation through compromised data. Recognizing the severity of these outcomes emphasizes the need for immediate action if a mistake is suspected, such as changing passwords and contacting Amazon support to report the incident. Quick response limits the damage and prevents scammers from deepening their hold on stolen information.
Equally important is educating oneself on the broader impact of such breaches, as stolen data can be sold or used in future attacks. Taking steps to secure other online accounts and monitoring financial statements for unusual activity can mitigate long-term risks. Turning a moment of vulnerability into a learning experience strengthens resilience against the relentless tactics employed by fraudsters.
Final Thoughts on Staying Safe
Reflecting on the journey through safeguarding against Black Friday phishing scams, the steps taken provided a comprehensive shield for Amazon shoppers. From recognizing deceptive communications to leveraging security tools and staying wary of AI-driven tricks, each action built a stronger defense against cyber threats. The effort to remain cautious amid the holiday rush proved essential in protecting personal and financial information. Looking ahead, shoppers were encouraged to stay informed about evolving cyber risks and adopt Amazon’s recommended practices as a habit beyond the holiday season. Sharing insights with family and friends multiplied the impact, creating a wider network of vigilant users. As technology advanced, so too did the need for continuous learning and adaptation, ensuring that future shopping experiences remained secure and enjoyable.