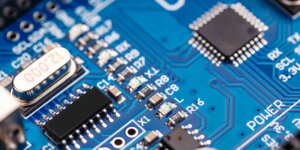
At the Apple September event, Apple made headlines with its announcement of the powerful A17 Pro chip, which powers the new iPhone 15 Pro and iPhone 15 Pro Max. One of the most notable features of this chip is its support for hardware ray tracing in mobile games, a groundbreaking development that promises to revolutionize the gaming experience on Apple