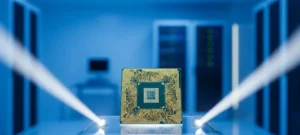
The persistent dominance of high-end graphics solutions in the enthusiast market has long necessitated a radical shift in engineering philosophy to challenge established industry monopolies effectively. As the sector moves beyond the iterative refinements seen in recent hardware cycles, AMD is preparing a “clean sheet” approach with its RDNA 5 architecture. This strategic pivot marks a departure from the conservative











